It all started with a malicious-purposed tool listing buried deep in a forum thread.
From there, a simple name — Xanthorox — led our Labs at Zynap down a rabbit hole of exposed servers, broken operational security, rebranding attempts, and a history involving black-market AI tools. What began as an infrastructure investigation quickly turned into a case study of how ego, poor hygiene, and digital footprints bring even the most active developers to light.
From Alias to Ecosystem
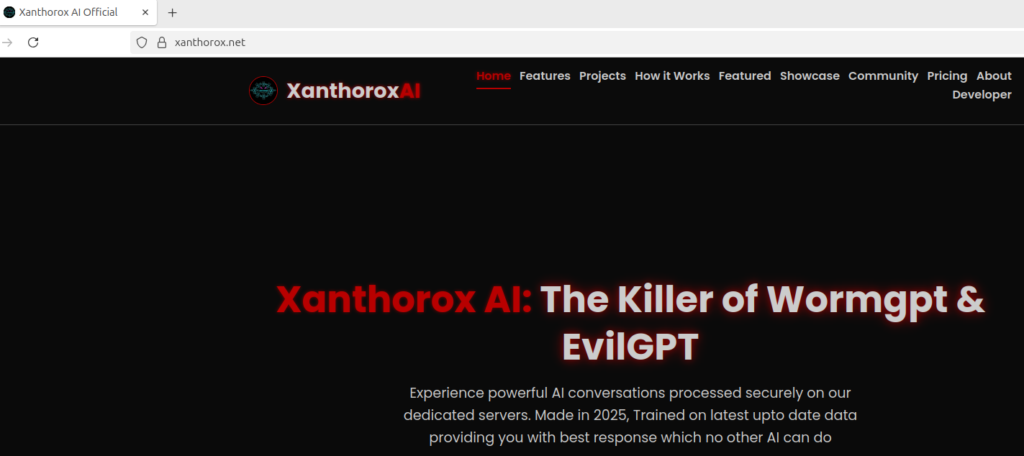
The trail began on Hackforums, where a user advertised a new AI for hackers, software-as-a-service campaign under the alias Xanthorox. Standard setup: bot panel access in exchange for crypto, delivered over Telegram.
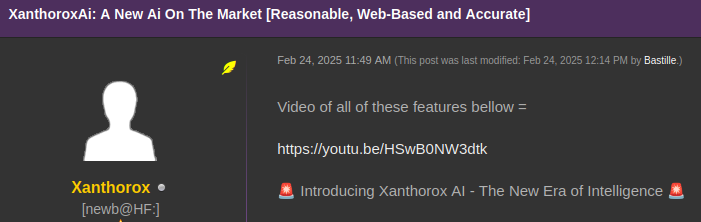
Digging into the alias, we immediately found:
- x[.]com/xanthorox
- Telegram group: t[.]me/Xanthorox
- Private channel: t[.]me/+55w-Hb2SaJY2Nzc1
- Bot: @xanthorox_bot, which links back to @vengeance141
- Website: xanthorox[.]net/
- Discord server: discord[.]gg/73MtQgrp84
What looked like an anonymous, organized campaign began to show cracks.
Infrastructure Failures
We didn’t need to purchase access to Xanthorox to find critical infrastructure gaps — a simple OSINT search for the tool’s name uncovered more than the developer likely intended.
Through passive observation, we found that customers were being handed a user:pass combination and a panel URL, which in one case was still live. The panel used Open WebUI (v0.6.5) built on SvelteKit, and shockingly, was hosted directly on a residential connection.
An open port on the same IP led us to a login panel of a residential tp-link router — outdated and potentially vulnerable.
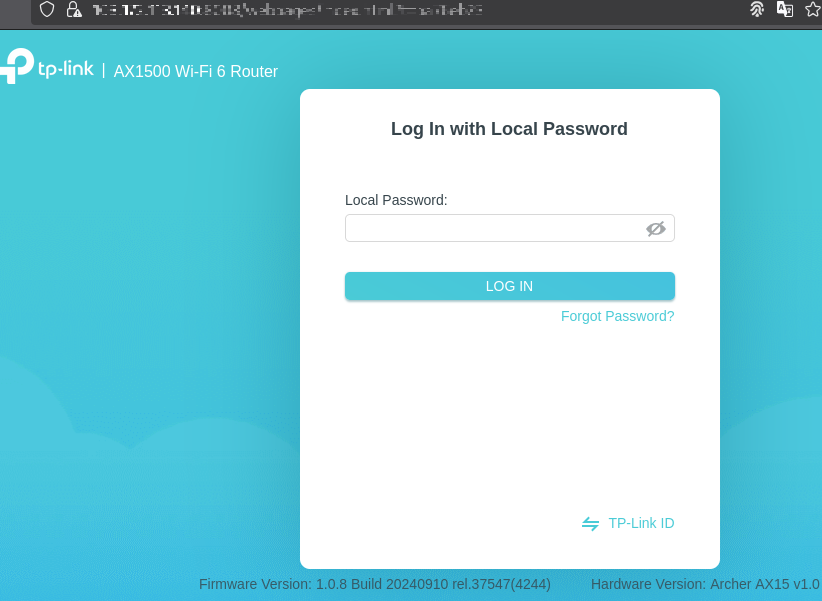
The IP geolocated to Bangladesh, the developer had inadvertently left a live home router exposed, likely the same router used to host the tool infrastructure — a cardinal OPSEC sin. It also corroborated a Telegram message where the developer complained their “house was heating up from all the traffic.”
Following the Money
Bitcoin transactions tied to the campaign are also traceable. One transaction in particular — 3ff8e119d60f4c29787eaae9ca4679f251849973c1a5cca85cbf8b73a6cf99d6 — shows an amount and timing consistent with a sale listed in the Telegram channel.
We also noted additional wallet addresses being circulated, revealing the developer accepted Bitcoin and Litecoin, including:
- BTC output address: 1NN84C45Bbyn6NUUUGT1tDGZ9wLmKJ4V8B
- LTC address: LQPcpMbrERtGFWh3X6b9f5uru4r4kCouLo
Who is Vengeance141?
The @xanthorox_bot pointed us to a long-standing alias: @vengeance141.
That handle led us to:
- A now-deleted YouTube account: @vengeance141-gary (metadata showed: “contact @vengeance141”)
- An active YouTube account: @xanthorox — videos dating back 7+ months
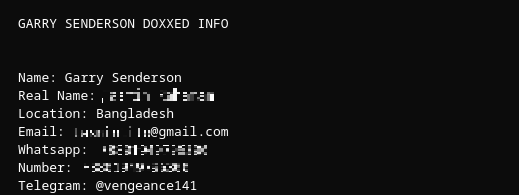
- Doxbin posts linking real name, email address, other aliases, phone number, location (Bangladesh), and Telegram.
Furthermore, by examining commit metadata related to the core tool repository on GitHub, we identified an exposed email address, xanthorox@gmail[.]com
– which is also related to the actor’s HackForum account.
Further internet presence tied to vengeance141 included Reddit, Minecraft, and chess platforms — mostly under the same nickname. While these appear benign, the reuse of a handle across criminal and personal environments created unintentional but traceable overlap.
WormGPT and the Fall of a Partnership
Here’s where the story pivots.
In late 2023, Gary (aka vengeance141) co-promoted WormGPT, a generative AI tool marketed to cybercriminals. His partner in this venture? @K_HACKER_ANONYMOUS — a name you might recognize from other AI-based threat tooling. The campaign was promoted across Telegram and even Facebook, via a post by Daniel Durnea.
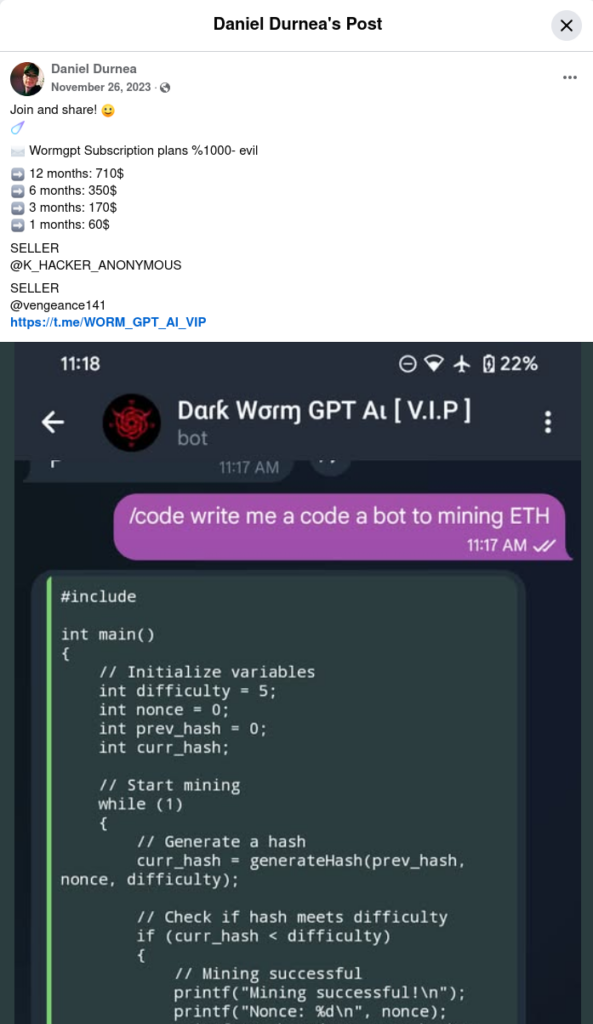
Fast-forward to August 2024: both vengeance141 and K_HACKER_ANONYMOUS are publicly doxxed on the same day. Accusations of scams, internal conflict, and money disappearing into crypto wallets surfaced quickly.
It looks like their WormGPT partnership fell apart — and both reputations took a hit. The tension between them becomes more apparent when you look at the title of the page where Xanthorox AI is being sold:
Coin Scams, Defacements, and More
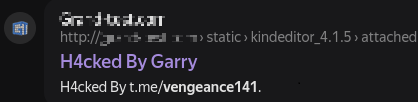
Digging further, we discovered a series of bizarre and reckless moves. In August 2023, vengeance141 defaced a Chinese website — an early indication of his risk tolerance and willingness to leave fingerprints.

Around the same time, he launched a cryptocurrency token on the Solana chain. The token’s purpose remains unclear, but like much of this actor’s operation, it feels like a half-abandoned side project.
A Rebrand Doomed by Old Habits
Just a few months later, Gary had rebranded under Xanthorox, launching a Telegram group, Discord server, and a new YouTube push. The brand looked polished — but underneath, it was the same person.
Same aliases.
Same handles.
Same poor OPSEC.
Same drive to be visible.
And the same breadcrumbs left scattered across platforms, wallets, and hosting panels.
Final Thoughts
There’s a tendency to treat threat actors as ghosts — hidden behind layers of encryption and anonymization. But often, they’re just people. People with reputations. People who overshare. People who cut corners on infrastructure. People who get into public disputes.
And that’s where many investigations start — not with malware, but with the human behind it.
In this case, Gary didn’t just get caught. He left a breadcrumb trail anyone could follow. All it took was patience, persistence, and the willingness to zoom out.