Preemptive cybersecurity is a Gartner-defined category. This is what it covers.
The Limits of Detect and Respond
An alert fires. The team responds.
That’s the model that MSSP and enterprise security programs run on. Managed detection and response, SOC-as-a-service, SIEM management: all of them are reactive by design. The workflow only starts when something triggers it.
That made sense in a slower threat environment.
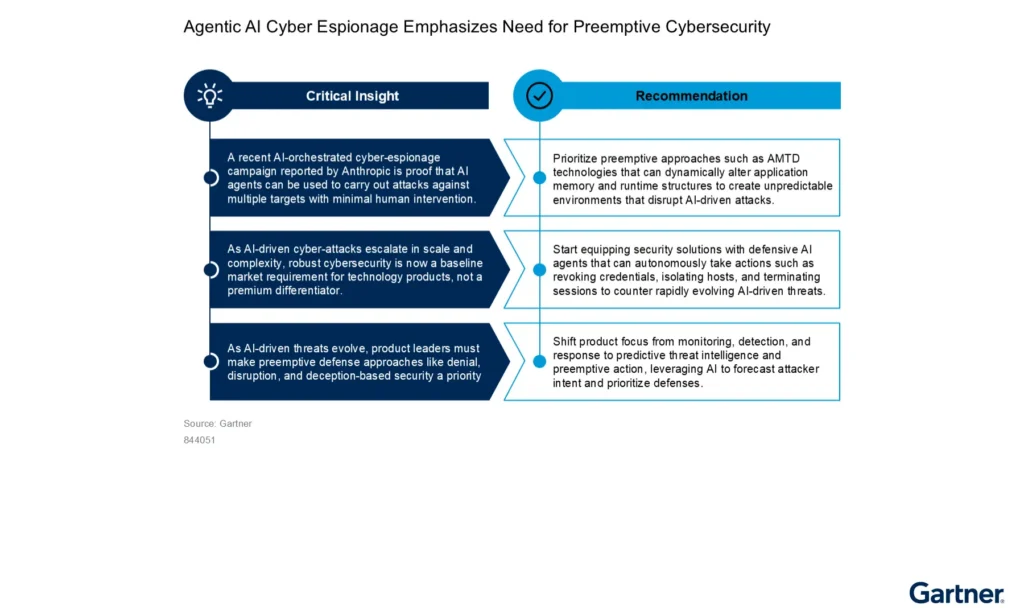
But AI-powered attack tooling has changed how fast vulnerabilities get exploited. So much so, that Gartner predicts there will be more than one million documented CVEs by 2030, up 300% from around 277,000 in 2025.
At that scale, detection-led approaches can’t keep up.
In its September 2025 press release, Carl Manion, Managing Vice President at Gartner, stated:
DR-based cybersecurity will no longer be enough to keep assets safe from AI-enabled attackers. Organizations will need to deploy additional countermeasures that act preemptively and independently of humans to neutralize potential attackers before they strike.
Carl Manion, Managing Vice President, Gartner. September 2025
Detect and Respond is a well-established approach. But it only ever starts once a threat has already reached your environment.
Gartner’s research is clear that this is no longer enough.
How Gartner Defines Preemptive Cybersecurity
In its Top Strategic Technology Trends for 2026, Gartner defines preemptive cybersecurity as an integrated, AI-driven approach that anticipates, denies, deceives, and disrupts attacks before they occur. It sits within three distinct security postures:
- Reactive Security: detects an incident after it has occurred and responds to it.
- Preventive Security: reduces the baseline attack surface through hardening, patching, and access controls.
- Preemptive Security: identifies signals of attacker intent and disrupts the attack before it is executed.
Understanding preemptive security also means understanding two terms it’s often grouped with: proactive and predictive. Each one describes a different level of how early and how autonomously security acts.
Proactive Security
Proactive security covers everything a security team does before an incident: patching vulnerabilities, hardening configurations, penetration testing, threat hunting, and access controls. Most security teams would describe themselves as proactive.
The honest limitation is that this work is largely human-driven, and the intelligence it produces often sits in reports and tickets that nobody acts on before the next incident arrives. Proactive security strengthens defenses, but relies on humans to act on the intelligence it produces.
Predictive Security
Predictive security goes further. It uses data, threat intelligence, behavioral analytics, and machine learning to forecast where an attack is likely to come from, which assets are most exposed, and which attacker techniques are most probable. It produces risk scores and early-warning signals.
The gap is that a forecast on its own doesn’t stop anything. If nothing automatically acts on the prediction, the security team is still waiting.
Preemptive Security
Preemptive security is where the forecast leads to automated action. Gartner’s research describes it as a shift from broad proactive defense to a targeted, predictive approach that identifies the precursors of an attack and intervenes before a breach occurs.
It takes that forecast and acts on it: denying access, deceiving attackers, disrupting attack chains, without waiting for a human to review anything.
The Difference Between Proactive, Predictive and Preemptive Security
The three approaches move from broad and manual to targeted and autonomous.
As Gartner puts it, every preemptive approach is predictive and proactive. But proactive and predictive approaches are not automatically preemptive.
Deny, Deceive, Disrupt: How Preemptive Cybersecurity Operates
Gartner structures preemptive cybersecurity around three operating principles, known as the Three Ds. Each one addresses a different way of stopping an attack before it causes damage.
Deny
Close off the routes an attacker would take before they get to use them. That means continuously discovering and validating exposures, automating remediation faster than any manual process can manage, and applying obfuscation that makes sensitive data and code invisible to reconnaissance tooling.
Deceive
Make it difficult for attackers to distinguish real assets from controlled environments. Automated Moving Target Defense (AMTD) continuously shifts network characteristics such as IP addresses, ports, and protocols to confuse attack tooling.
Advanced cyber deception deploys honeypots, synthetic credentials, and fake infrastructure to divert attackers, generate behavioral intelligence, and surface attacker presence before any real system is reached.
Disrupt
Interrupt the attack chain in its early stages. Unlike detection and response, disruption in the preemptive model does not wait for an incident to be confirmed. It acts on early behavioral signals automatically, without waiting for human authorization. This is what allows preemptive security to operate at the speed modern attacks demand.
The Five Capabilities That Define Preemptive Cybersecurity
Preemptive cybersecurity isn’t a single product you deploy. It’s a set of capabilities that work together, each addressing a different phase of the attacker’s timeline. Gartner identifies five core technologies in its preemptive security framework. The value isn’t in any one of them individually. It’s in the security orchestration.
Predictive Threat Intelligence
Analysis of adversary behavior, infrastructure signals, and exposure data to forecast likely attack vectors before indicators of compromise appear. It informs action before an attack is in motion.
Automated Moving Target Defense (AMTD)
Continuous modification of the attack surface to remove the stable reference points that automated attack tooling depends on. When network characteristics shift dynamically, reconnaissance data becomes stale before it can be weaponized.
Advanced Cyber Deception
Deployment of decoy assets, synthetic identities, and fake infrastructure. Attackers who interact with deception environments reveal their presence, their tools, and their methods before reaching real systems. Passive monitoring cannot produce that kind of intelligence.
Continuous Threat Exposure Management (CTEM)
Gartner’s CTEM framework treats exposure management as an ongoing program, not a quarterly audit. It continuously identifies, prioritizes, and validates real exposures across internal and external attack surfaces, so remediation stays focused on what matters.
Advanced Obfuscation
Concealing code, data, and system configurations from attackers who have achieved partial access. Obfuscation limits what an attacker can exploit even after an outer layer has been breached, and disrupts the automated tooling that modern attacks rely on to move quickly.
By 2030, preemptive cybersecurity solutions will account for 50% of IT security spending, up from less than 5% in 2024, replacing standalone detection and response as the preferred approach to defend against cyber threats.
Gartner, September 2025
Why the Market Is Moving to Preemptive Cybersecurity
The market is already moving.
And by 2030, Gartner expects 75% of today’s detection and response solutions to have preemptive capabilities built in. The providers that don’t move in that direction have a two to four year window before clients start looking elsewhere.
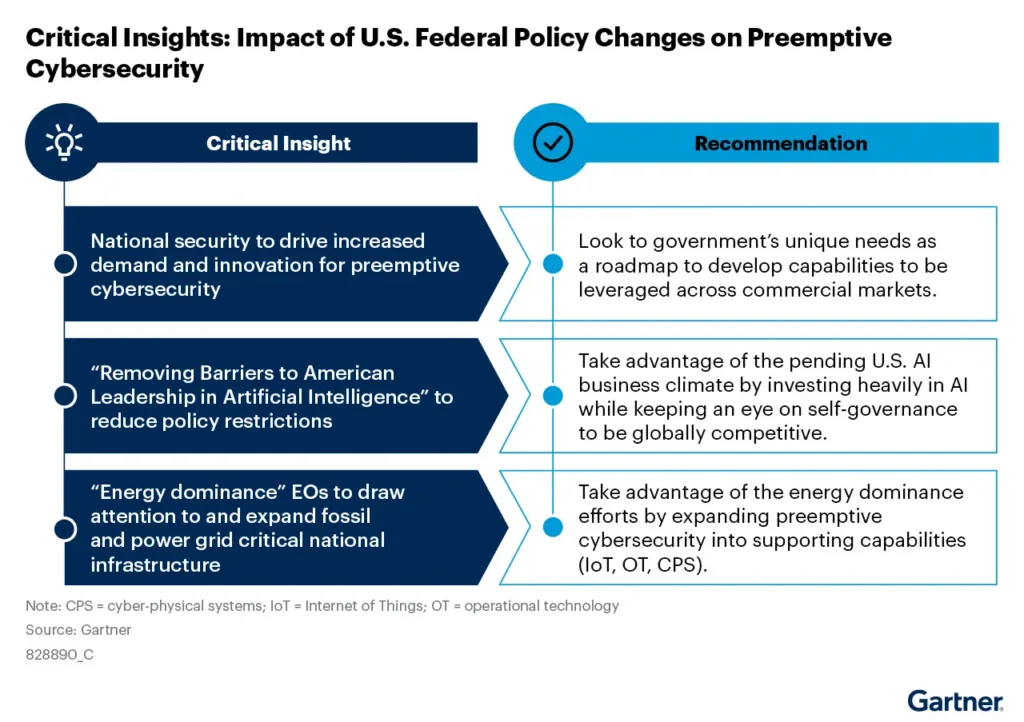
The shift is happening beyond commercial markets too. Gartner’s analysis of U.S. Federal policy shows that national security requirements are accelerating preemptive cybersecurity development. What gets built for government tends to reach commercial markets next. For MSSPs, that means the capabilities coming to market are already being tested against the most demanding security environments anywhere.
Looking further out, Gartner has introduced the concept of the Autonomous Cyber Immune System (ACIS): a defense that runs itself, continuously, without waiting for human instruction. It’s early-stage, and it shows where the category is heading.
What This Means for MSSPs
For MSSPs, preemptive cybersecurity changes both how you operate and what you can offer clients. We cover the full operational model in detail in our guide to how MSSPs scale revenue without staff augmentation.
Growing Revenue Without Growing the Team
Most MSSP service portfolios are built around monitoring, detection, and response. As clients start asking about preemptive security, the conversation with their providers changes. The focus moves from how fast you respond to whether you can prevent the incident in the first place.
Preemptive automation changes the unit economics here: when workflows act on threat intelligence before incidents form, alert volume across the client portfolio drops. Fewer incidents per analyst means more clients, without burning out the team or missing SLAs. Playbooks built once deploy consistently across every client environment.
The commercial impact is measurable:
- 20-35% Improvement in Operating Margin Per MDR Client
- 2x Clients Managed Per Analyst With No SLA Degradation
- 40-60% Revenue Growth Without Proportional Headcount Growth
The revenue upside comes from what those analysts do with their freed capacity. When automated workflows handle triage, enrichment, and initial containment across the portfolio, senior analysts have time for higher-margin work: managed threat intelligence, proactive credential monitoring, and offensive security simulation.
These are the service lines that grow revenue per client and strengthen an MSSP’s proposition.
Building Preemptive Security Into Your Service Portfolio
Preemptive security is becoming part of what clients expect from their managed security providers. And MSSPs that can deliver it are in a stronger position.
Building preemptive capabilities into a service portfolio changes the nature of what an MSSP offers. Managed detection and response is increasingly a commodity. Preemptive security, delivered well, commands a different conversation.
See how Zynap works for MSSPs.
What This Means for Enterprise Security Teams
For Enterprise security teams, the preemptive shift changes two things.
Alert Fatigue and Analyst Capacity
Security operations centers are built on human judgment. The problem is how much of that judgment gets spent on noise. When analysts are triaging hundreds of alerts per shift, the ones that need attention get less time than they deserve.
Preemptive workflows change that by acting on threat intelligence before incidents form, so fewer alerts reach the queue in the first place.
Acting Before the Alert Fires
The gap between an attacker gaining access and a detection workflow identifying them is where damage happens. Preemptive approaches close that gap by monitoring adversary infrastructure, dark web signals, and credential exposure continuously. They act on those signals before an incident forms.
For Enterprise security teams, the measurable outcomes are:
- 40-70% Fewer Irrelevant Detections Reaching the Analyst Queue
- 20-40% Fewer Incidents That Escalate to Containment
- 50-70% Improvement in Mean Time to Detect (MTTD)
- 30-45% Reduction in Mean Time to Respond (MTTR) Within 90 Days
- Equivalent of 1-2 Senior FTEs of Recovered Capacity Per 10-Person Team
These aren’t small improvements. When analysts aren’t buried in reactive triage, they have time for the work that needs them: complex investigations, threat hunting, and decisions that require real experience.
See how Zynap works for enterprise security teams.
The Role of the Preemptive Security Orchestrator
Each of the five capabilities above covers a different phase of the attacker’s timeline. Together, they create a defense that operates before an incident begins. The challenge is connecting them, taking intelligence from one source and turning it into action in another, at machine speed, consistently. That’s preemptive security orchestration.
Zynap is built as a preemptive security orchestrator. It brings together the core capabilities of the preemptive model, predictive intelligence, offensive validation, continuous exposure management, deception, and AI-driven automation, coordinating them into a system that acts before attacks begin.
Orchestrating preemptive security requires a clear understanding of a category that most organisations are still early in. For enterprise security teams and MSSPs, that process is just beginning.
The frameworks exist and the technology is real. For those who engage with it now, while it’s still taking shape, there’s a genuine advantage. For those who don’t, there’s a gap that will only get harder to close.
Further Reading From Gartner
Gartner: Preemptive Cybersecurity Is the Future of Security, September 2025. gartner.com
Gartner: Top Strategic Technology Trends for 2026. gartner.com
Gartner Webinar: Preemptive Cybersecurity, a Top 5 Disruptive Trend for 2025. gartner.com/webinar
Gartner Article: Preemptive Cybersecurity Solutions. gartner.com
Gartner: Tech Innovators in Preemptive Cybersecurity. gartner.com
