Introduction
Ignite your curiosity one last time as we peel back the curtain on the dark art of credential theft! In our first post of this series, we charted the scope of the credential theft epidemic—1.2 billion compromised accounts analyzed by platform, password strength, and geography—revealing who’s most at risk.
The second post took us deep into the underground supply chain, exposing how cybercriminals rent infostealers and command-and-control infrastructures, leverage hosting and evasion services, manipulate YouTube SEO for malware distribution, and organize professional “traffer” crews to streamline operations.
Now, in this final chapter, we pivot to the ultimate question: how do cybercriminals turn stolen credentials into profit? From reselling cloud-hosting resales and pay-per-hit schemes to turnkey account-takeover services, subscription-style botnets, and affiliate-style resale markets, we’ll dissect some of the most notable examples. We’ll compare payout models across underground marketplaces and criminal hierarchies, quantify the return on investment that keeps these operations alive, and expose the financial mechanics driving the credential theft economy.
Join us as we close the loop on the credential theft cycle and illuminate the monetization engines that keep it running.
Revenue streams
Telegram clouds
Picking up on the discussion about the Traffer teams, comes the Telegram clouds. If we consider that resulting stealer logs can then be sold via these subscription-based platforms, it becomes clear how profitable these campaigns can be. Let’s inspect some examples:
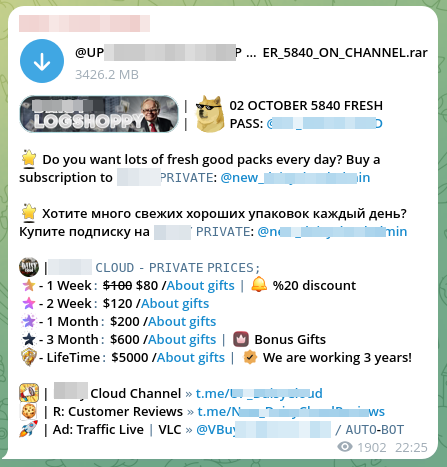
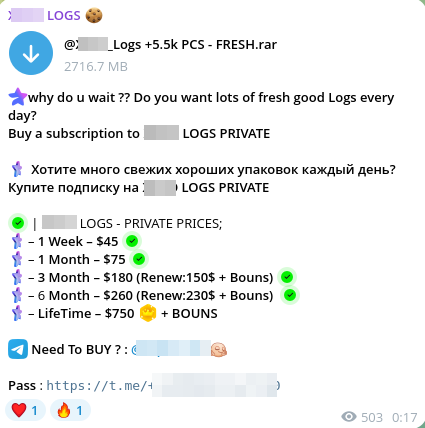
Telegram clouds have emerged as dedicated marketplaces for stolen data. Operating on a subscription model, they provide continuous access to exfiltrated logs, much like streaming services, regardless of individual usage. Fees range from weekly or monthly rates to lifetime access, creating steady revenue streams for operators (see Extra services for an in-depth discussion on prices).
The emergence of Telegram clouds signals a professionalization and commoditization of credential theft. No exfiltrated information is wasted: credentials not immediately exploited by traffers can still be monetized in bulk through cloud subscriptions. As a result, Telegram clouds now occupy a central role in the credential theft cycle, bridging the gap between raw log theft and underground resale.
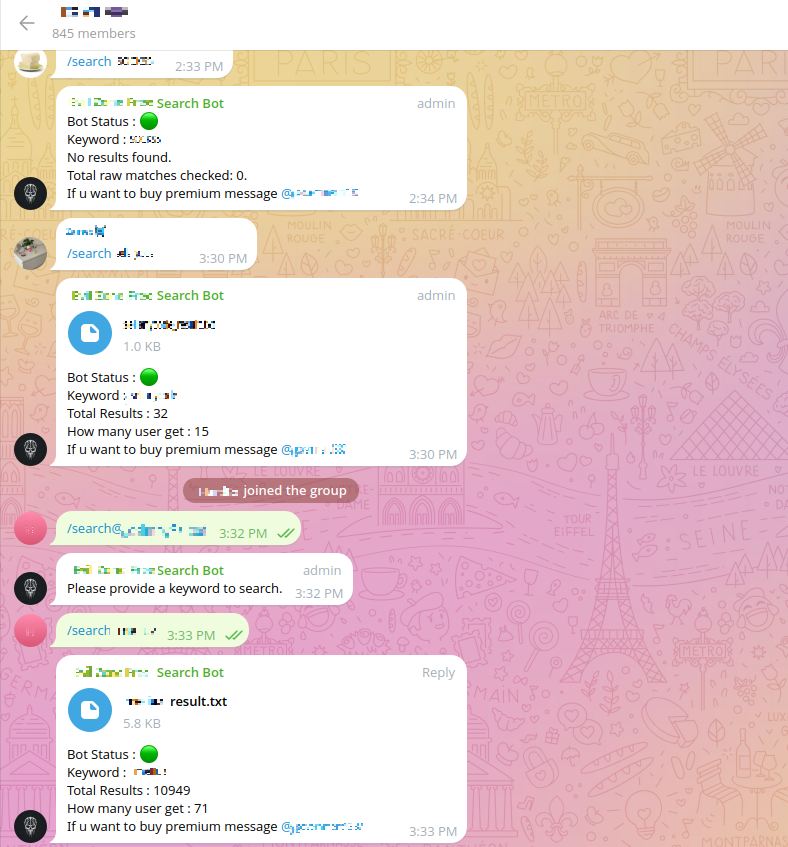
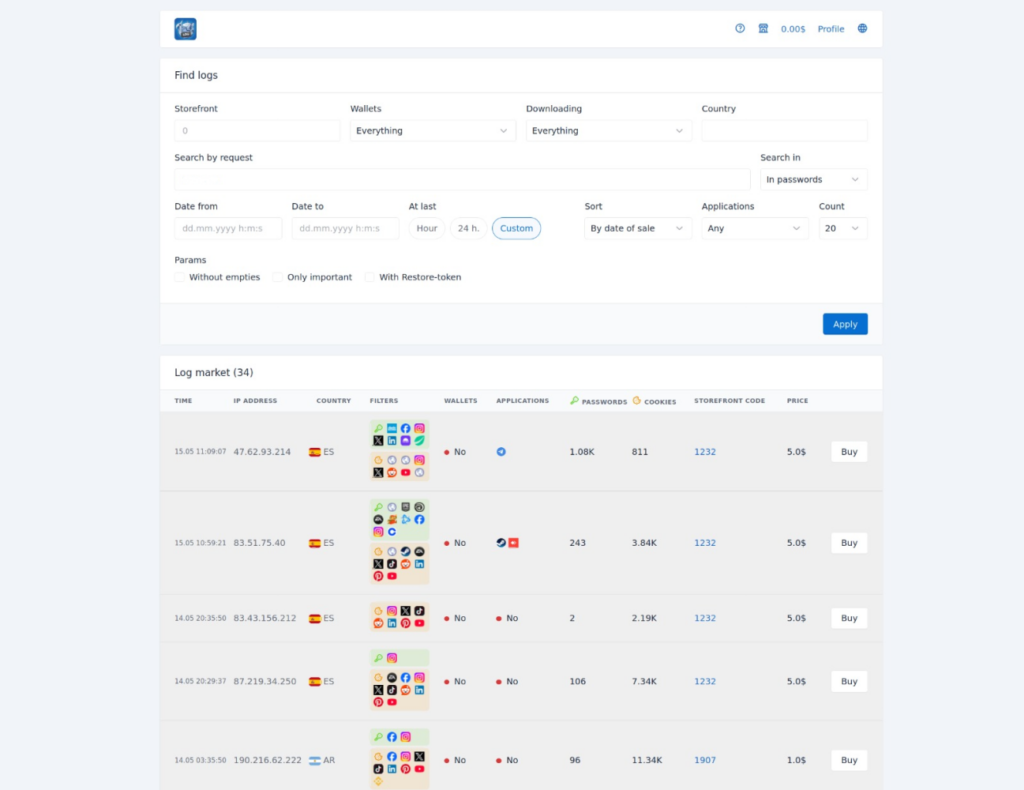
Direct sales
In the first half of 2025, Zynap analysts observed a new trend emerge in the credential theft ecosystem. Forget the old model of Telegram cloud monthly subscriptions for bulk data. Now, buyers can target exactly what they need, selecting specific logs through automated bot storefronts, maximizing precision.
In parallel, we followed the brief rise (and swift takedown) of Lumma Market: a pioneer log marketplace built and operated directly by the malware’s own developers.
This vertical integration marked a significant evolution, with the same actors profiting from both the infections and the resulting data sales. The operation, including the malware infrastructure and shop, was seized by law enforcement in May.
In another illustration of the trend, we have observed logs stores with dedicated websites:
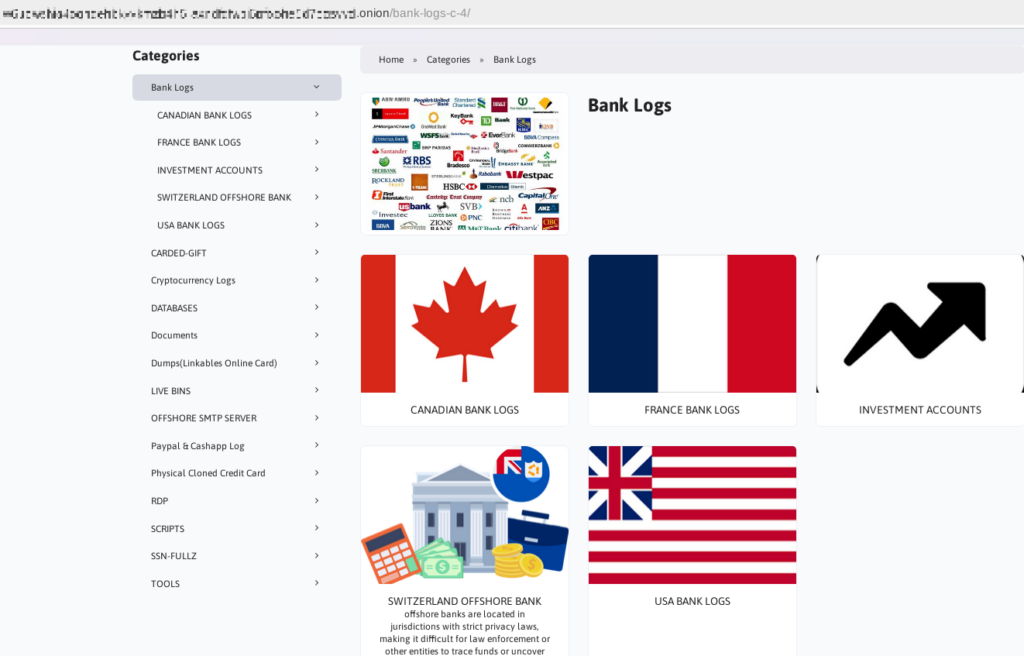
In this case, once the buyer selects a target country, they are prompted to choose a bank and are then offered accounts with different access details, such as email logins, passwords, two-factor authentication codes, and PII.
The credential theft market is no longer defined by a single business model. Traditional bulk subscription services on Telegram clouds continue to exist, but they now share space with more selective marketplaces that let buyers purchase precisely what they want. There have also long been centralized card-and-data hubs such as RussianMarket or BidenCash that catered to stolen-payment-card sales; these platforms were created and run by private intermediaries who bought or rented malware from others, listed the harvested data, and took a commission—they were not operated by the malware developers themselves.
Earlier markets functioned as static repositories of stolen data, but newer platforms integrate automated checkers, filters by geography or service type, and other tools that make purchases more efficient.
At the same time, the relationship between suppliers and buyers has shifted: what once depended on individual sellers now increasingly involves operators of the malware themselves, moving toward vertical integration and cutting out intermediaries. This evolution also reflects an economy of risk: decentralized hubs distribute liability across many small actors, while integrated models concentrate both profit and exposure in fewer hands.
The rise of experiments like Lumma Market and specialized storefronts selling bank and account logs illustrate these dynamics, revealing a diversified underground economy where both mass access and precision sales coexist, offering multiple paths to profit.
Account valuation in the underground economy
Telegram
Telegram cloud subscription pricing shows clear patterns, but also striking contrasts depending on frequency, platform, and subscriber base. We’ve followed around 25 clouds over months to extract some stats and observed the following standards in subscription pricing schemes:
- Weekly average: US$56
- But watch out for the extremes: US$15 vs. US$250.
- Monthly average: US$132
- The gap here is also quite evident: US$30 at the low end and a hefty US$550 at the top.
- Lifetime average: US$500
- Not all clouds offer lifetime subscriptions.
- Smaller clouds often offer 3-day access instead, which costs around US$10.
- Number of subscribers: from niche (40 subscribers) to massive reach (22,730 subscribers), averaging about 3,400 subscribers per cloud.
Our analysts have proposed several hypotheses to explain the significant variation in prices. First, certain exclusive clouds may offer higher-quality or novel credentials, which could drive prices upward. In some cases, logs flow directly from malware into the cloud in real time, without intermediaries; these sources tend to command higher prices due to immediacy and exclusivity.
Conversely, the resale of older credentials might reduce their value, resulting in lower-quality offerings at lower prices.
Another factor could be the volume and frequency of shared credentials, which may influence subscription costs. Finally, the price of infostealers (the initial source of infections leading to credential acquisition) may also shape the overall pricing structure. At this stage, there is no definitive explanation. Price disparities may stem from a combination of these factors or potentially from influences not yet identified.
We also note that there are both generalist clouds and specialized clouds, with different pricing structures depending on their focus. Some clouds are dedicated exclusively to Hotmail accounts, others offer mixed datasets, and still others specialize in cookies:
- Hotmail-specific clouds:
- Weekly: steady at US$30–$40
- Monthly: predictable at US$75–$100
As observed, Hotmail clouds clearly sit in a lower-cost segment, with weekly and monthly plans priced over 50% below the general market average.
It’s also worth noting that subscriber count does not necessarily translate into higher or lower prices. Factors such as market longevity, brand reliability, and product quality often carry more weight than sheer popularity, meaning that even services with fewer subscribers can command premium pricing if they deliver trust and consistent value.
Finally, and most importantly, if the monthly subscription to these clouds is approximately US$132, and these clouds have thousands of subscribers, the profitability of credential theft campaigns becomes evident.
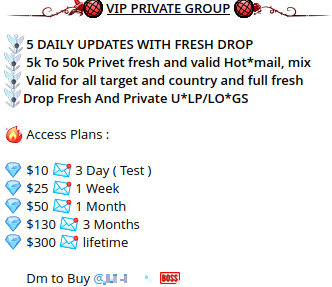
Dedicated websites
This type of marketplace operates at a boutique level, making it more exclusive both in offerings and in pricing. While a cloud subscription providing access to thousands of generic logs can be purchased for as little as a few hundred dollars, targeted bank account logs — particularly from holders in developed countries with higher average balances — command much steeper prices. The logic is straightforward: the greater the potential for profit, the higher the price.
However, such purchases also demand more technical skill and operational maturity from buyers. These are not simple login-password pairs for gaming or streaming accounts; they are high-value financial accounts closely monitored by banks and more likely to trigger scrutiny from fraud teams or even law enforcement. As a result, actors willing to pay these premiums are typically more experienced attackers with the resources and expertise to exploit them effectively.
Taking the example from the shop in Figure 6, bank log prices ranged from as low as US$100 to as high as US$10,000 per account, largely tied to the available balance. At the top end, a US$10,000 listing corresponded to an account holding US$700,000, while the US$100 accounts were linked to balances of roughly US$1,500–US$2,000. This demonstrates the clear correlation between account liquidity and underground valuation, as well as the market’s appetite for precision-targeted, high-yield opportunities.
Partial conclusions
Overall, the data highlights how subscription models vary not only in price but also in the scale of audiences they attract, reminding us that pricing strategies must balance affordability with market reach.
Buying credentials
For those who obtain credentials but are not sure how to capitalize on them, whether due to inexperience, limited resources, or a small-scale operation, there is the option to sell them to larger, more structured groups. These actors specialize in repackaging and monetizing stolen credentials at scale.
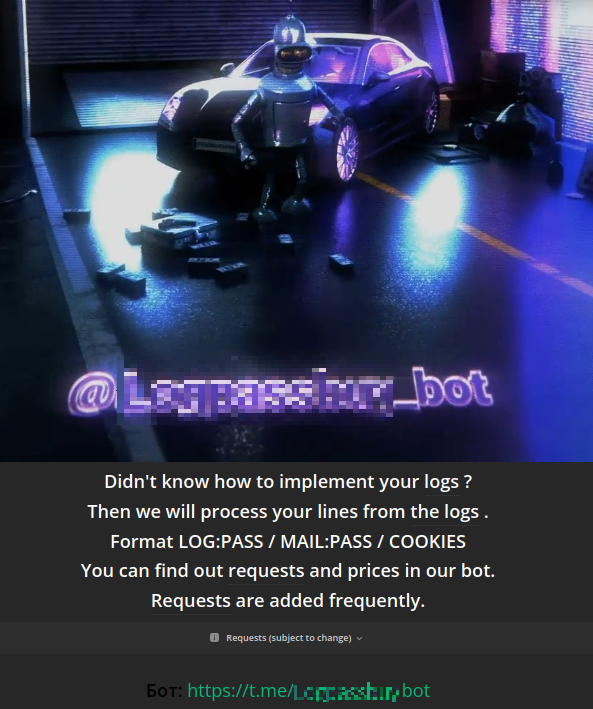
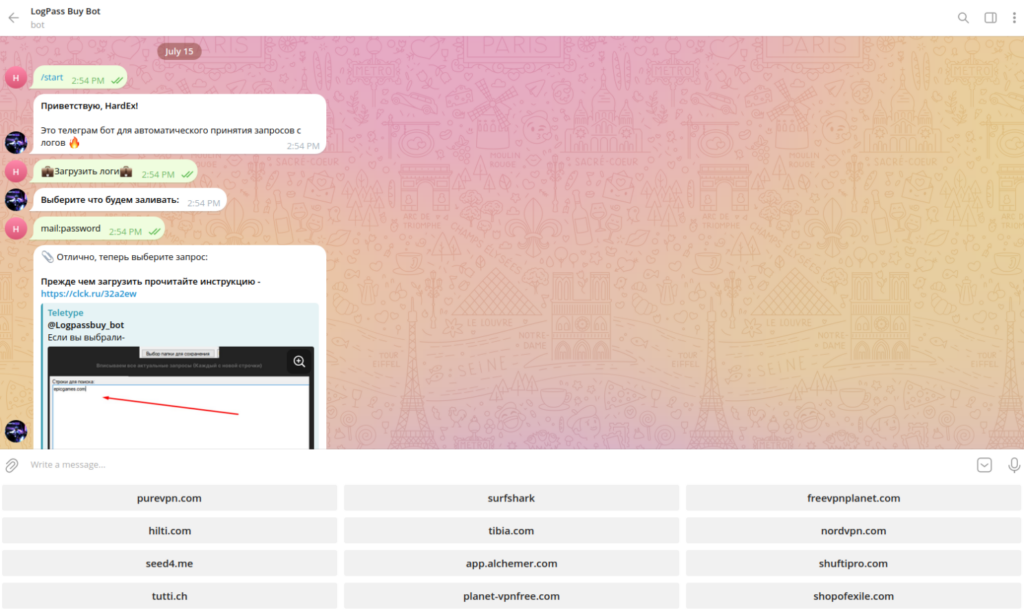
In the example above, the actor openly shares a full list of services they buy logs from. After classifying these services, we found that their main interest lies in credentials from the following categories:
- VPN and anonymization services – 34% (some of which are displayed in the figure above)
- E-commerce – 22%
- Email and web access providers – 16%
- Digital identity verification – 12%
- Data aggregators and enrichment services – 9%
- Survey collection tools – 3%
- Gaming – 3%
Interestingly, as we continued monitoring the “logs” section of underground forums, we identified multiple other buyers following similar models — acquiring specific credentials across a wide range of services, including gaming, social media, email, crypto exchanges, and others. These credentials are bought for as low as US$0.10 per combination of login and password, depending on the affected service and value it implies. The categories percentage displayed above is only an example of one specific actor, and it doesn’t reflect the general interest of all logs buyers in the underground economy.
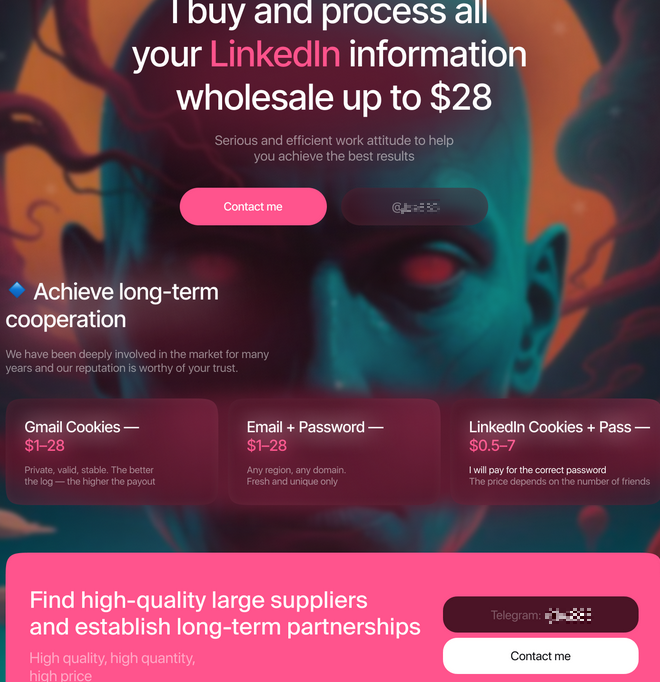
The trade in stolen credentials has evolved into a layered supply chain: small actors sell to larger groups that repackage and monetize at scale. Demand often centers on services like VPNs, e-commerce, and digital identity, which enable further fraud or obfuscation. While exact preferences differ, the persistence of specialized buyers shows that virtually any stolen credential can find a market.
Extra services
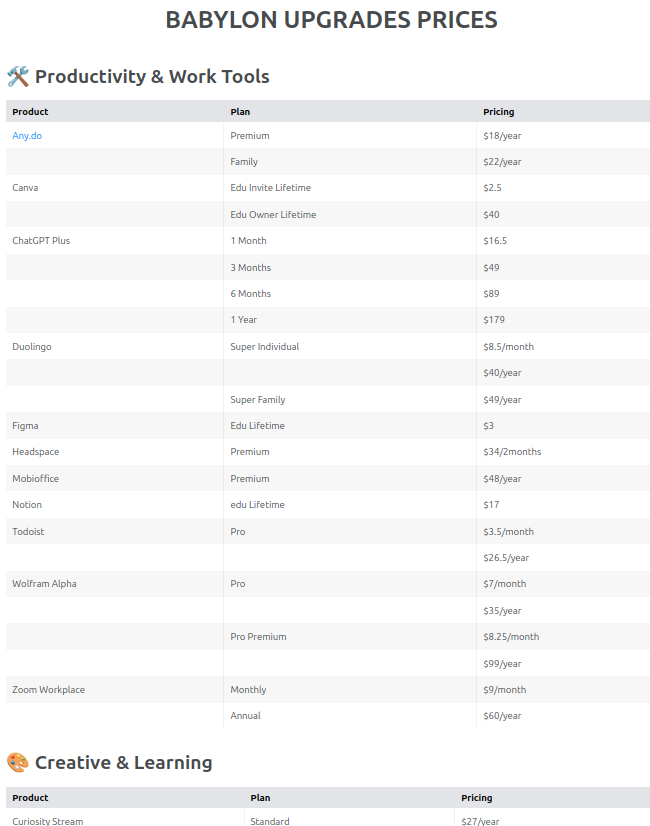
An emerging trend observed within Telegram clouds is the expansion of offerings beyond shared credential access. These marketplaces increasingly advertise subscriptions to a broad range of services, including video/music streaming platforms, productivity software, and Artificial Intelligence tools.
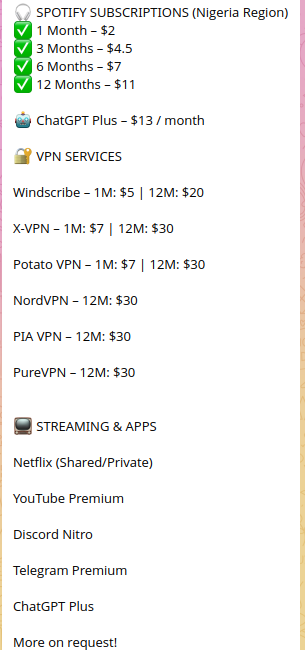
As shown in the figures above, entire bundles of such services are made available. This suggests that actors are not only trading in raw credentials but also actively filtering and repackaging them into marketable products. By extracting access linked to specific, high-demand services, they resell subscriptions at prices well below official market rates, effectively creating parallel underground economies.
Campaign take downs
In late October 2024, a joint operation by the Dutch National Police, the FBI and Eurojust’s Joint Cybercrime Action Taskforce, dubbed Operation Magnus, dismantled the infrastructure behind two major infostealers, RedLine and META (active since 2020 and 2024, respectively). Authorities seized command‑and‑control servers in the Netherlands, disabled distribution domains and affiliate Telegram channels, and arrested key facilitators. Both malware families operated on a Malware‑as‑a‑Service model: affiliates purchased builder licenses, customized payloads, and spread them via phishing, malicious ads and counterfeit downloads to harvest saved passwords, browser cookies, cryptocurrency wallets and system fingerprints, then sold the resulting logs in underground markets.
Following on the heels of Operation Magnus, from midMarch to midMay 2025 Microsoft’s Digital Crimes Unit, alongside the U.S. Department of Justice, Europol’s EC3, Japan’s JC3, and industry partners, launched Operation Endgame, securing civil and criminal orders to seize over 2,300 malicious domains and shut down five additional control panels used by the Lumma Stealer (active since 2022). The malware, like its predecessors, was offered in tiers (from basic builds to fullsourcecode licenses) marketed through Telegram and Russian language forums. Victims were lured via spear phishing, malvertising and fake CAPTCHA pages, exposing passwords, banking credentials, credit card data and cryptoseed phrases for resale.
These coordinated takedowns exposed how fixed infrastructure such as command-and-control servers, distribution domains, and resale marketplaces can be dismantled by cross border law enforcement action. By seizing not only the malware itself but also the forums, broker channels and domains that support it, authorities have struck at every layer of the underground economy. Remarkably, these weren’t shortlived nuisances but sustained operations running for 2-4 years. Keeping an infostealer service alive at scale for that long reflects a high degree of technical skill, effective affiliate management and real resilience against lawenforcement pressure.
Conclusion
Cybercriminals monetize stolen credentials through subscription “clouds,” precision storefronts, resale chains, and even vertically integrated markets like Lumma. Profitability is strong even under conservative assumptions: while a cloud with 3,400 subscribers at US$132/month could gross US$500,000 monthly, in reality only a fraction are paying customers. Even if just 10–20% convert, operators can still net five-figure revenues every month.
Targeted banking logs add another lucrative tier, with individual accounts priced between US$100 and US$10,000 depending on balances, while bulk credentials acquired for pennies per log are resold at far higher margins. These models show that credential theft doesn’t just pay off, it pays off reliably across different scales and market niches.
Behind the sales channels are the mechanisms that transform stolen data into spendable money. Money mule networks, cryptocurrency mixers, prepaid cards, and gift card schemes provide cash-out options, while automation tools such as credential checkers, config marketplaces, and CAPTCHA-solving services drive efficiency and scale. This industrialization lowers the entry barrier for low-skill actors while maximizing returns for organized groups. Even after large-scale takedowns like Operations Magnus and Endgame, the ecosystem proves resilient, quickly decentralizing and mirroring its infrastructure to sustain revenues.
Ultimately, credential theft fuels more than resale markets: it underpins account takeovers, business email compromise, ransomware operations, and synthetic identities. Its low entry costs, high margins, and adaptability ensure it remains one of the most profitable and persistent pillars of cybercrime. By tracing the lifecycle from theft to monetization, laundering, and resilience, it becomes clear why credential theft is not a passing threat but a cornerstone of the underground economy.