Three trends define the current landscape:
Stealer logs have overtaken traditional credit card data as the most strategically valuable commodity, driven by their ability to bypass two-factor authentication through session hijacking. The underground economy operates as an integrated supply chain, from malware infection to credential theft to marketplace listing to ransomware deployment, with dark marketplaces serving as the central storefronts where stolen data is monetized at scale. And the Chinese-language dark web remains a significant and undermonitored threat vector, with platforms that differ substantially from Western counterparts in both operational model and product focus.
The underground economy continues to demonstrate significant resilience. Markets that are seized or disrupted are rapidly replaced or restored, following a cycle that shows no signs of slowing. This report profiles the six most significant active marketplaces and provides context on the broader ecosystem that sustains them.
The Underground Ecosystem
How It All Started
Underground markets first gained prominence with Silk Road in 2011, the first dark web marketplace to operate on the Tor network. While Silk Road primarily facilitated drug sales, it demonstrated that an anonymous marketplace could function at scale. Following its shutdown in 2013, markets have continued to appear and be taken down in a persistent cycle. The financial incentives are considerable: Empire Market facilitated over $430 million in illegal sales between 2018 and 2020 before its operators were convicted in June 2024 (U.S. Immigration and Customs Enforcement, 2024). However, law enforcement action against individual platforms has not disrupted the broader ecosystem. Each takedown is followed by user migration, the emergence of new platforms, and the reconstitution of the marketplace environment within weeks.
How They Operate
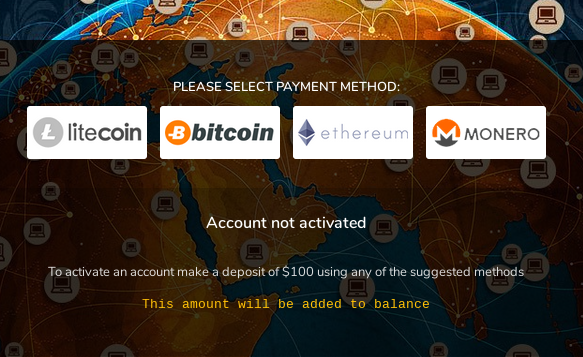
Most marketplaces are accessed through the Tor browser via .onion domains, though some also operate on the clearnet through rotating mirror URLs. Registration models vary from simple username-and-password forms to mandatory deposits or invitation codes, and these access barriers serve as a deliberate design choice that shapes each market’s user base. All transactions are conducted in cryptocurrency (Bitcoin, Monero, Litecoin, or USDT), and platforms maintain buyer-seller trust through escrow systems and dispute resolution mechanisms. Underground forums, particularly those in the Russian-speaking cybercriminal community, function as the social infrastructure surrounding these markets. These forums are where marketplace reputation is established, platform reliability is debated, and users coordinate migration when a marketplace is disrupted.
What Gets Traded
Stealer logs have become the most valuable commodity in the underground economy. These consist of data harvested from infected computers by infostealer malware (e.g. RedLine, RaccoonStealer, Vidar, LummaC2). A single log can expose dozens of accounts, including corporate credentials and session cookies that bypass two-factor authentication. Prices range from $0.20 to over $300, with freshness and the value of credentials contained within driving the price variation.
Stolen financial data remains a foundational product category: credit card numbers (CVVs), magnetic stripe dumps used for cloning physical cards, and Fullz, which are complete identity profiles that enable fraud ranging from opening bank accounts to applying for loans. Prices range from under $1 for basic CVVs to $200+ for premium dumps.
Corporate network access constitutes the highest-priced product category listed on dark web marketplaces, and the one with the greatest potential for organizational damage. Sold by Initial Access Brokers (IABs), these listings provide direct entry into compromised organizations, typically via RDP (remote desktop control), VPN (virtual private network access), or SSH (command-line server access). Prices range from hundreds to tens of thousands of dollars depending on the target’s size and sector, reflecting the potential for downstream damage: a single access listing can serve as the entry point for ransomware deployment, data exfiltration, or espionage. These listings frequently appear on marketplaces days to weeks before an actual attack against the target organization.
The Marketplace as a Supply Chain
These products move through a supply chain in which dark marketplaces serve as the central storefronts. Infostealers infect machines, the resulting logs are listed on marketplaces, and buyers extract corporate access to either exploit directly or resell to ransomware affiliates. At each stage, value increases. Threat actors have been observed specifically searching through marketplace listings for logs containing access to sensitive corporate environments, purchasing low-cost logs that may ultimately facilitate six-figure ransom payments. Telegram serves as a complementary distribution channel where several marketplaces announce new inventory, but the marketplaces themselves remain the transactional core where stolen data is monetized at scale.
A notable growth strategy within this ecosystem is the large-scale data giveaway, pioneered by BidenCash, a credit card marketplace that operated from 2022 until its seizure by the U.S. Government in June 2025 (U.S. Attorney’s Office, Eastern District of Virginia, 2025). BidenCash distributed over 12 million stolen credit cards for free across multiple giveaways, building one of the largest user bases in the underground economy. This strategy has since been adopted by newer market entrants, and BidenCash’s trajectory (rapid growth, extensive reach, and eventual law enforcement takedown) represents a characteristic lifecycle pattern for aggressive underground marketplaces.
The Major Dark Marketplaces
The Established Giants
BriansClub
In 2019, BriansClub was compromised by an unknown actor who exfiltrated 26 million stolen credit card records and provided them to KrebsOnSecurity. Subsequent analysis by Flashpoint determined that over 14 million of those records were valid (Krebs, B. (2019). The platform continued to operate and expand following the incident.
This resilience is a defining characteristic of the platform. Operational since 2014, BriansClub has been the longest-running credit card marketplace in the underground economy, with an estimated 400 million+ cards listed over its lifetime and reported revenues exceeding $126 million. When the platform experienced significant operational disruption following U.S. sanctions against its payment infrastructure, (Krebs, B. (2024) it became the most discussed topic across underground forums for weeks. Users continued requesting news and working domains months after the disruption, and when the platform was eventually restored, the degree of user retention confirmed its entrenched position in the ecosystem. The profitability of its model has since led to the emergence of multiple clones attempting to replicate its operations.
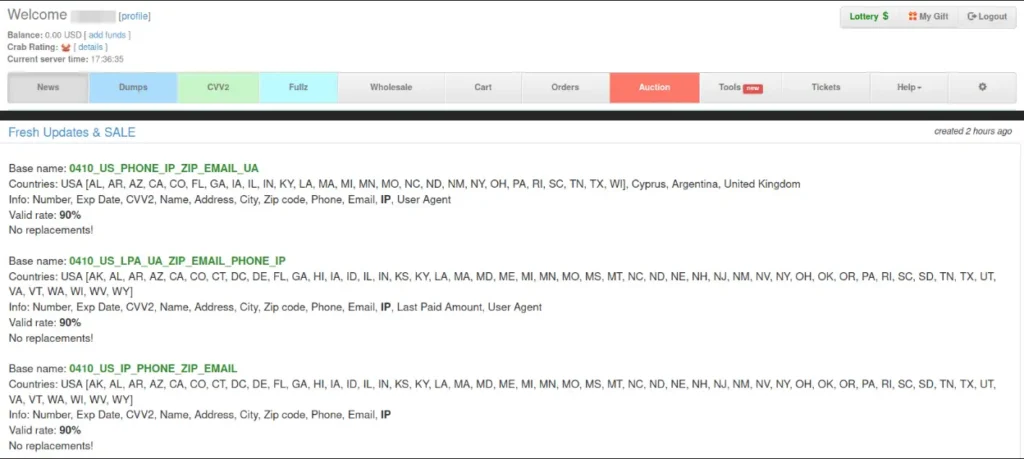
A notable characteristic of BriansClub is its lack of official presence on any underground forum, which distinguishes it from virtually every other major marketplace. Its reputation has been built entirely through word of mouth and over a decade of consistent service delivery. Dumps (magnetic stripe data used to clone physical cards) range from $1 to over $200, with a “Wholesale” tab available for bulk purchases. CVV data (card number, expiration date, and security code) is listed at $1–$150, and Fullz (full identity profiles including name, address, and Social Security number) are priced between $14.95 and $59.95. The marketplace also maintained recurring lottery jackpots offering discounts and market credit to incentivize continued participation, though no lottery has been conducted since August 2024, which may indicate reduced administrator engagement. The origin of BriansClub’s data inventory remains undetermined, as the platform does not allow users to sell on it, and its sourcing methods have not been disclosed.
RussianMarket
RussianMarket functions less as a traditional marketplace and more as a broker, connecting sellers of stolen data to buyers through a searchable, automated interface. Founded in 2019, the platform has established itself as a primary source for stealer logs and login credentials, with consistent references across underground forums as a reliable data supplier. Sellers can bulk-upload logs that become immediately searchable, and buyers can filter results by specific credential types prior to purchase, providing a high level of operational efficiency in the transaction process.
The platform requires a $100 mandatory deposit for entry, one of the highest barriers in the ecosystem, which positions it as a marketplace oriented toward committed buyers. Its reputation within the underground community is predominantly positive, though one recurring concern has been documented: users allege that the platform occasionally presents publicly available logs as private or exclusive data. In the stealer log market, freshness and exclusivity constitute the primary value proposition for buyers, and the discovery that purchased data was already in wide circulation directly undermines platform credibility. Forum discussions regarding RussianMarket reflect this tension: while the platform maintains a generally positive reputation, the data quality concern remains a recurring topic.
The Rising Challengers
B1ack Stash
B1ack Stash has adopted the growth strategy pioneered by BidenCash (seized June 2025) (U.S. Attorney’s Office, 2025), leveraging large-scale data giveaways to establish credibility and acquire users. Launched in April 2024, the platform immediately released over 1 million stolen credit card records for free, directly replicating the approach that had built BidenCash into one of the largest underground markets. In April 2025, B1ack Stash escalated its promotional activity with a giveaway of more than 4 million cards, demonstrating both significant data acquisition capabilities and an intent to establish a dominant market position.
However, the platform’s growth has been accompanied by notable trust concerns. The administrator has faced multiple accusations of fraudulent activity across forums and has responded by publicly confronting dissatisfied customers. The visible disputes have generated documented trust concerns across multiple underground forums.
The marketplace experienced its first significant law enforcement action in September 2025, when the Manhattan District Attorney’s Office seized 12 domains associated with B1ack Stash for trafficking over one million stolen cards (Manhattan District Attorney’s Office, 2025). The platform reappeared on new mirrors shortly after, consistent with the resilience patterns observed across other marketplaces following similar enforcement actions. The platform’s continued operation is subject to both sustained law enforcement pressure and ongoing trust deficits within the underground community.
STYX Market
In contrast to B1ack Stash’s promotional approach, STYX Market has grown without freebies (bulk distributions of stolen records used as a promotional strategy), official forum accounts, or aggressive marketing since its launch in 2023. The platform has built its user base entirely through product availability and community reputation, earning positive assessments from multiple cybersecurity research publications over the past year.
The platform maintains a high operational tempo, with new product listings posted on a near-daily basis and a news section updated several times per month. Its catalog is diverse: stealer logs range from $0.20 to over $300, database packages are listed at prices up to $1,700, and a premium private section provides access to exclusive data for $500 lifetime or $300 plus $25 monthly. Vendors are required to undergo screening before listing products, a quality control measure that differentiates STYX from marketplaces with open seller registration.
The platform’s sustained growth without promotional activity has occurred within a stealer log market where buyers increasingly prioritize data quality and exclusivity over price.
Exodus Marketplace
Exodus Marketplace is the most recent entrant profiled in this report, with a reputation that has been subject to significant scrutiny across underground forums. Since beginning its promotional activity on major Russian-speaking underground forums in October 2024, the platform has built a growing user base, initially through the distribution of free invitation codes and subsequently through a paid access model requiring a deposit (increased from $20 to $30) to access log listings.
The platform’s reputation concerns extend beyond typical data quality issues. Multiple users have reported non-functional or low-quality logs across various forums. Additionally, a job posting published in March 2024 advertising a system administrator position was subsequently reported by several users to have been designed to harvest personal information rather than fill a legitimate role. These incidents have generated sustained skepticism within the underground community regarding the administrator’s operational intentions.
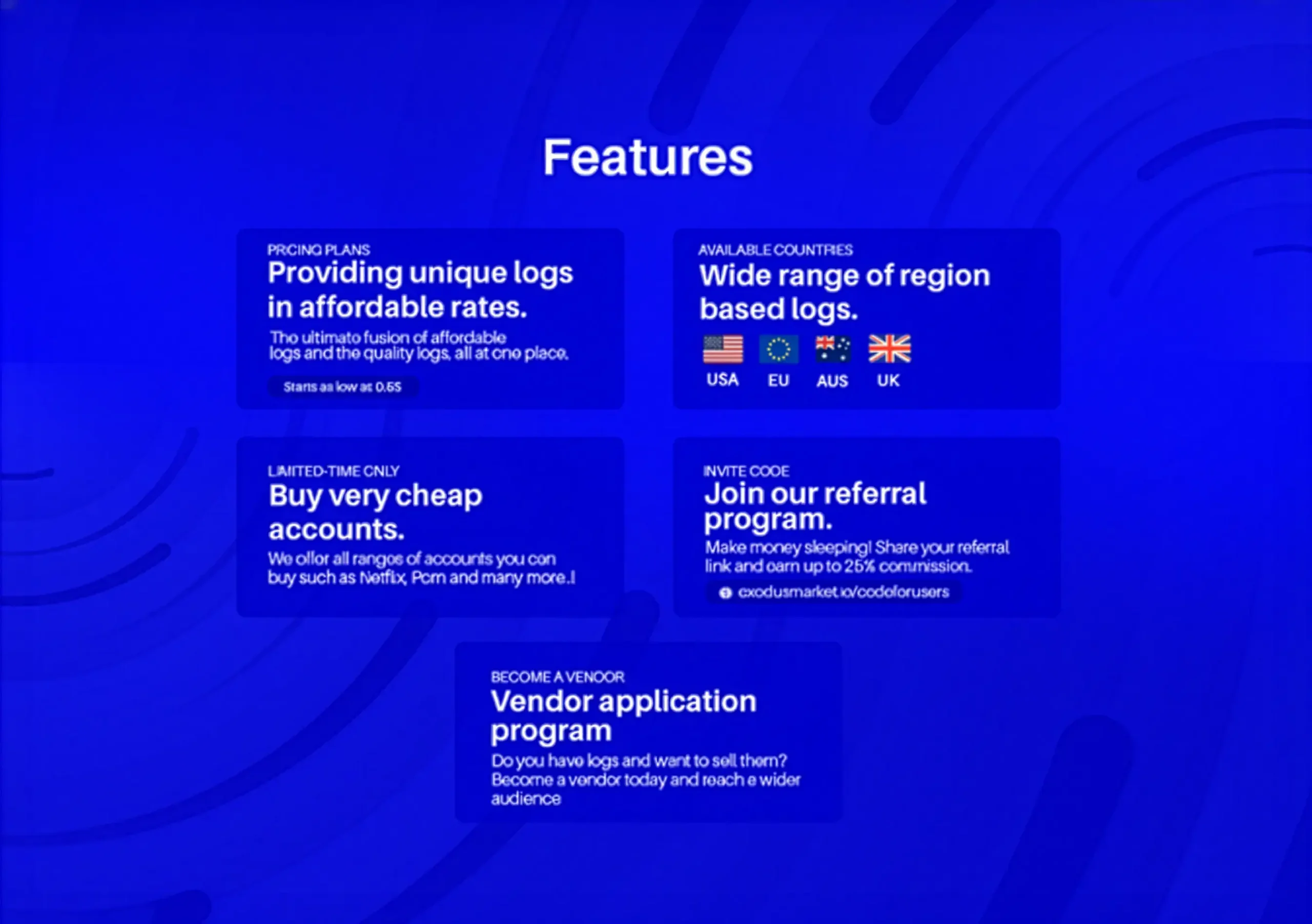
The platform has continued to develop its infrastructure despite these concerns. In June 2025, Exodus launched its own dedicated forum in which discussions can be locked by the administrator and private messaging between users is disabled, maintaining full visibility over all communications. The impact of this transparency model on user trust has not yet been established, and the platform’s trajectory continues to be subject to significant uncertainty.
The Chinese Outlier
DeepMix
DeepMix represents a fundamentally different model from the Western marketplaces profiled in this report. As the dominant platform in the Chinese-language dark web, it operates on numeric IDs, public-only communication, and mandatory payments for posting or commenting. It is one of the longest-running underground marketplaces globally, with 12+ years of continuous operation in an environment where most platforms are disrupted within a few years.
Originally launched as the “Chinese Darknet Forum” in 2013, the platform began as a privacy-focused discussion community for Chinese-speaking users. By 2015–2016, responding to demand for cryptocurrency-based transactions, it was restructured into a full-scale marketplace. In 2019, a sustained DDoS attack took the platform offline for several weeks. Rather than ceasing operations, it resurfaced with enhanced protections, reinforcing its reputation for operational resilience.
The security model is built on radical transparency and deliberate friction. Users are assigned a numeric ID with no custom usernames permitted. Three separate passwords are required: login, transaction, and recovery. All communication with sellers occurs through public comments, ensuring that every transaction and dispute is visible to the entire community. The platform uses Litecoin with built-in coin mixing for transaction privacy, operating exclusively through Tor across 11 onion links.
The product categories reflect characteristics specific to the Chinese cybercriminal ecosystem. The dominant category is virtual resources: hacking tools, gambling applications, and developer tools. Physical items are uncommon due to the traceability risks associated with shipping. The primary value lies in the data category: stolen PII, leaked databases, financial institution data, and WeChat stolen data, a product category specific to the Chinese market with no direct equivalent on Western platforms. In contrast to Western darknet markets where drugs frequently represent a primary category, Chinese platforms are dominated by leaked data and virtual goods, a distinction shaped by China’s Great Firewall and the scale of its digital economy.
The platform’s market position was challenged in 2022 when a rival called Chang’an was launched and gained rapid traction. The resulting dispute exposed the inherent fragility of trust within the underground economy. Each side accused the other of fraud: the newcomer alleged forced username changes and excessive fees against long-standing users, while the established platform claimed its competitor had compromised user account passwords. By April 2023, multiple users reported being unable to access their funds or accounts. Neither side provided verifiable evidence, but the mutual accusations resulted in measurable erosion of trust across both platforms.
As Western markets face increasing scrutiny from the FBI, Europol, and allied agencies, Chinese-language platforms represent a growing gap in threat intelligence coverage. With a 12-year operational track record and a distinct security model, this marketplace constitutes a priority for monitoring, particularly for organizations with exposure to the Asia-Pacific region.
Conclusion
The dark web marketplace ecosystem continues to demonstrate a high degree of resilience against law enforcement operations. The cases examined in this report, including the restoration of BriansClub following its 2024 takedown, the rapid reappearance of B1ack Stash after a domain seizure, and the three-year operational span of BidenCash prior to its June 2025 seizure, confirm that disruption of individual platforms does not translate into disruption of the underlying economy. Migration to alternative platforms occurs rapidly, and the operational model persists regardless of which specific marketplaces are active at any given time.
A significant shift in the commodity landscape has been observed. Stealer logs have displaced traditional credit card data as the highest-value product category, driven by their capacity to bypass modern authentication mechanisms through session hijacking. The marketplaces experiencing the most sustained growth, notably STYX and RussianMarket, are structured around this product category. Concurrently, large-scale data giveaways have been established as an effective market entry strategy, as demonstrated by both BidenCash and B1ack Stash.
Trust infrastructure remains a critical factor in marketplace longevity. Escrow systems, public dispute resolution, vendor screening, and loyalty mechanisms all contribute to sustaining buyer engagement. When these mechanisms fail, as observed in the dispute between DeepMix and its competitor, the resulting erosion of confidence extends beyond the platforms directly involved. Underground forums continue to function as the primary trust and coordination layer, and a marketplace’s standing within these communities frequently determines its viability more than the platform’s own capabilities.
A notable gap persists in the monitoring of Chinese-language dark web platforms. DeepMix has maintained operations for over 12 years under a fundamentally different model, yet it receives considerably less analytical attention than its Western counterparts. As law enforcement pressure on English and Russian-speaking markets increases, this coverage gap is expected to widen. The underground economy functions as an integrated supply chain, from initial malware infection through credential theft to ransomware deployment, and detection at any stage of this chain can disrupt attacks before they reach their final objective.
Zynia Labs
This report is part of Zynia Labs’ ongoing threat intelligence research. For more from the team, take a look here.
References
Krebs, B. (2019). “BriansClub” Hack Rescues 26M Stolen Cards. https://krebsonsecurity.com/2019/10/briansclub-hack-rescues-26m-stolen-cards/
Krebs, B. (2024). U.S. Indicts 2 Top Russian Hackers, Sanctions Cryptex. https://krebsonsecurity.com/2024/09/u-s-indicts-2-top-russian-hackers-sanctions-cryptex/
Manhattan District Attorney’s Office. (2025). Seizure of domains selling stolen credit cards. https://manhattanda.org/manhattan-d-a-s-office-seizes-domains-of-websites-selling-more-than-1-million-stolen-credit-cards/
U.S. Immigration and Customs Enforcement. (2024). Dark web marketplace owners charged with facilitating $430M in illegal goods sales. https://www.ice.gov/news/releases/dark-web-marketplace-owners-charged-facilitating-430m-illegal-goods-sales
U.S. Attorney’s Office, Eastern District of Virginia. (2025). BidenCash marketplace domains and funds seized. https://www.justice.gov/usao-edva/pr/us-government-seizes-approximately-145-criminal-marketplace-domains