This is the story of how the operator of Ankarex, a smishing-as-a-service platform, was traced from an anonymous GitHub profile to a real name, a real city, and a real family using nothing but open-source intelligence.
Starting From a Single Account
The investigation began with a GitHub account: notsafety. No tip-off, no leaked database pointing to it, just a username and some repositories worth examining.
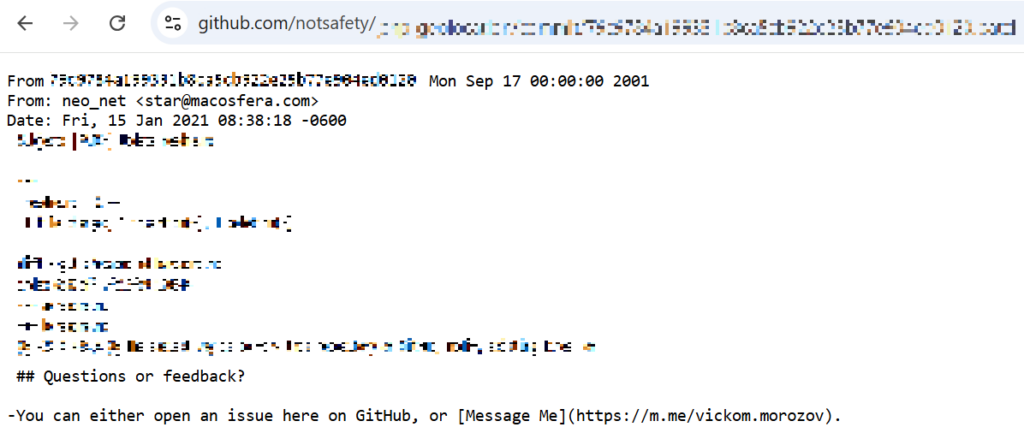
The first step with any GitHub account is to inspect the commit metadata. Most people don’t realize that every Git commit contains a name and email embedded in it. Not the GitHub display name, but whatever the developer configured locally on their machine. It’s something most people set up once and never think about again.
The commits from notsafety revealed two identities:
- From: neo_net <[email protected]>
And in older commits:
- From: Vickom Ishlovenko <[email protected]>
That gave us three things to work with: a handle (neo_net), a likely fabricated name (Vickom Ishlovenko), and an email address ([email protected]). But the real breakthrough came from something even more careless. In one of the older project files, the subject had left a message:
“message me at m.me/vickom.morozov”
That’s a direct Facebook Messenger link. And that single breadcrumb turned out to be the thread that unraveled the entire operation.
The Facebook Attribution Chain
Running criminal operations online requires strict separation between operational aliases and personal identity. A Facebook Messenger link embedded in your own code is the opposite of that.
A search for the vickom.morozov and Vickom Ishlovenko handles revealed an inconsistency: historical tags associated with Mexican users. The names “Vickom Morozov”/”Vickom Ishlovenko” sound Eastern European, but the social circle was entirely Mexican.
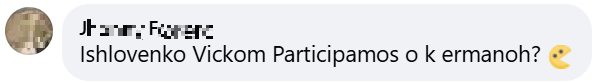
Digging further revealed a consistent group of Facebook friends who had tagged various iterations of the same handle over the years. The subject had changed their Facebook display name multiple times, cycling through “Vickom Morozov,” “Vickom Ishlovenko,” and other variations, but the underlying account remained the same. Friends tagged different names across different periods, but every one of them redirected to the same profile.
That profile belonged to Daniel H******.
The Facebook profile also listed a romantic partner (N.L.) and a sister (A.G.), whose handle contained “H*****” and whose listed location was Monterrey, Mexico.
The sister’s profile independently confirmed both the surname and the city, without relying on any of the subject’s own accounts.
The Bulgarian Who Wasn’t
This is a good moment to talk about the fabricated identity, because it held up for over a decade (at least on the surface).
The subject had built an elaborate Eastern European persona across multiple platforms. On a developer network, they claimed to be from Varna, Bulgaria. The names “Morozov” and “Vickom” are Slavic. Everything was carefully constructed to point away from Latin America.
But the technical evidence told a completely different story. Two residential IP addresses, obtained from separate data breaches, both geolocated to Monterrey, Mexico, on different ISPs, which rules out a VPN coincidence. A phone number from a gaming retailer breach carried a Monterrey area code. Language settings in every breached account were set to Spanish. And the Facebook social graph, as described above, was organically and unmistakably Mexican, and more specifically pointing to Monterrey.
The cover story was designed for people who wouldn’t look underneath, but the moment anyone checked the metadata, it collapsed.
Breach Data Convergence
The Facebook chain was strong, but attribution requires independent corroboration and that’s where breach data came in.
The starting point was the fabricated name from the GitHub commits: “Ishlovenko Vickom.” Searching for that name across breach data surfaced a hit in an Instagram leak, a record mapping the name “Ishlovenko Vickom” to the username nebulacrypt and, crucially, to a new email address: [email protected]. Same domain as the GitHub commit email ([email protected]), but a different mailbox. That single pivot – from a fabricated name to a second email on the same domain – unlocked the rest of the breach data chain.
Searching for [email protected] revealed it had been registered via Facebook under the name “Vickom Morozov,” closing the loop back to the Facebook identity. It also appeared in several other data breaches, the most significant one being from a Mexican gaming retailer, which mapped that email to the name Daniel H*****, a Monterrey-area phone number, and a location consistent with all other indicators.
The same email appeared in a music streaming service breach, where the account had been registered via Facebook OAuth, independently tying [email protected] to the Facebook identity. The breach record also included a date of birth field (November 6, 1996), gender (male), and country (Mexico), though the date of birth remains unverified and should be treated as a hypothesis rather than a confirmed finding; a breached password, sonic1996, used on another account provides a weak supporting indicator, as it may reference a birth year. So, at this stage, the evidence picture included:
- Two fully independent sources confirming the name “Daniel H*****” (Facebook social graph + gaming retailer breach)
- Two residential IPs geolocating to Monterrey
- A phone number with a Monterrey area code
- A family member whose Facebook profile independently lists Monterrey
- A possible date of birth suggested by breach data (unverified, with the password sonic1996 as a weak supporting indicator)
The attribution was solid.
Sixteen Aliases, One Pair of Shoes
Going back to approximately 2013, accounts on gaming platforms, developer communities, and social networks could all be linked through a web of shared email and IP addresses. The subject used at least 16 different aliases over the years*, including variations of “Vickom Morozov,” “Vickom Ishlovenko,” “neo_net,” and “Ankarex.”
The linking methodology is straightforward in principle but can be tedious in practice. An email address appears in one breach tied to alias A. The same email appears in a different breach tied to alias B with an IP address attached. That IP shows up in a third breach tied to alias C, which uses a different email. That email appears in yet another breach under alias D. And so on, until the web covers sixteen names across dozens of platforms.
What made this subject easy to track was a consistent behavioral pattern: change the display name, keep the underlying account. Change the alias, keep the same email domain. Move to a new forum, reuse the same residential IP. It’s the OPSEC equivalent of changing disguises every day but wearing the same shoes, a pattern covered in more depth in our .
*A full listing of all known aliases and associated email addresses, along with their sources, is provided in the appendix at the end of this post.
Connecting the GitHub Identity to the Underground
One critical link still needs to be established: how do we know the person behind the GitHub account notsafety is the same person running Ankarex on underground forums?
The bridge is the neo_net handle. GitHub commits directly tie neo_net to the [email protected] email. Searching for neo_net revealed the same handle active on multiple underground forums where it was used interchangeably with the Ankarex handle. On at least two forums, both handles belonged to the same registered user, promoting the same Telegram channels and the same platform domains (ankarex[.]io, ankarex[.]net).
The GitHub repositories provide further corroboration. The subject’s repos include self-authored JavaScript validators for credit cards, IBANs, and national ID numbers, plus a PHP geolocation script for fingerprinting website visitors, the same components that the Ankarex platform uses operationally. Before launching Ankarex as a paid service, the subject had released a deprecated Santander phishing kit for free on underground forums. The post included working code, installation instructions, and the comment: “Antibots are old, so don’t bother me with problems.” This was the old version, and the current one would cost money, a classic move in underground economies: give away an older version to build reputation, then monetize the upgrade. The timing is also notable: the last public GitHub activity was in 2022, the same year the Ankarex platform became commercially available.
The forum presence is broad. The neo_net and Ankarex handles appeared across Breached, Cracked, Patched.to, XSS, BHF, Leakzone, Nulled, and Hackforums. The subject also maintained a personal Telegram account (@neo_net), several channels — @Ankarex (currently inactive), @Ankarex_Announcements (also inactive), and the current active channel, which migrated from @AnkarexNews – and a support bot. The migration pattern across Telegram channels mirrors the alias rotation seen everywhere else.
That’s the full bridge: GitHub commits to neo_net, neo_net to the forums, forums to Ankarex. This is what connects the technical identity to the criminal operation with high confidence.
Inside the Ankarex Platform
Ankarex operates as a smishing-as-a-service platform, which is essentially a SaaS product where the service being sold is phishing infrastructure. Customers deposit cryptocurrency, then use the platform to launch SMS phishing campaigns against desired targets.
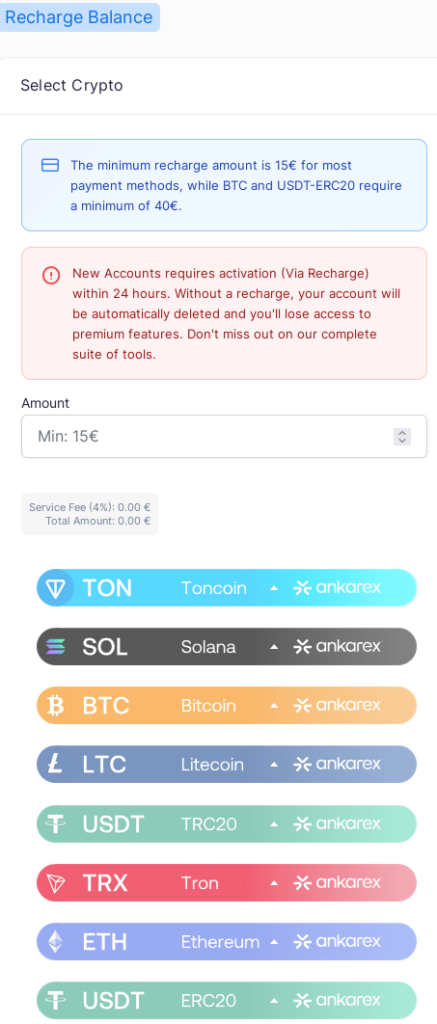
The platform accepts eight cryptocurrencies through rotating single-use wallet addresses, making wallet-based attribution difficult. Analysis of the platform’s API responses and frontend code pointed toward a known commercial cryptocurrency payment gateway as the backend processor, assessed with medium confidence based on matching payment ID formats, API field naming conventions, and transaction status terminology.
The financial OPSEC is notably more competent than the personal OPSEC. All payment API calls are proxied server-side (the browser only communicates with the Ankarex domain), and the rotating wallet design prevents simple address-based tracking. It’s an interesting contrast: careful enough to proxy API calls, careless enough to leave a Facebook Messenger link in a project file.
An Associate Surfaces
One tangential thread is worth mentioning. The Santander phishing kit that neo_net released on forums was hosted on Google Drive. The Drive file metadata revealed the uploader’s Google account email, which turned out to belong to an alleged separate individual, a Spain-based phishing operator running their own bank-impersonation domains targeting different financial institutions. Whether this person is an operational associate, someone who hosted the file on the subject’s behalf, or even another identity controlled by neo_net himself remains unclear. It’s a single point of intersection with no further corroborating evidence, so the connection is assessed as low confidence. But it shows how one sloppy upload can potentially connect actors in these ecosystems.
What This Case Illustrates
Beyond the technical specifics, this investigation maps a trajectory that threat intelligence analysts encounter regularly. The subject started as a teenager in gaming communities around 2013. By 2016, they were active in developer circles.
By 2019, they were collecting offensive hacking tools.
By 2020, they had pivoted to fraud-specific tooling.
By 2022, they were operating a commercial cybercrime platform.
Curiosity becomes capability, and capability eventually finds a way to make money. The subject’s registration on a legitimate Mexican peer-to-peer lending platform in 2019 is a small but potentially telling detail; it may suggest financial pressure or, at minimum, an interest in financial systems that preceded the pivot to fraud. It’s also worth noting that the platform currently requires a Mexican credit bureau score, proof of income, and a bank account in the applicant’s name; if those requirements were in place at the time of registration, this would independently confirm Mexican residency and financial identity.
This isn’t the first time neo_net‘s operations have been publicly documented. In 2023, another piece of research was published exposing parts of the infrastructure and operational patterns behind the Ankarex platform. Despite that exposure, the service is still running, as the Telegram channel was last updated at the time of writing (February 2026). What has changed is the subject’s behavior, as neo_net has become noticeably more discreet, with less public forum activity and more careful operational security.
This raises an open question: is the original operator still behind the platform? There is no evidence that definitively proves or disproves it. The operation could still be run by Daniel H*****, or it could have been handed off to someone else. What we can say with confidence is that the person who built it is no longer anonymous.
For all the effort that went into the Bulgarian cover and the Ankarex platform, what actually gave him away was basic stuff. Same email domain everywhere. A Facebook link left in a project file. A social graph he never bothered to separate from his real one.
A single line of text in a forgotten file, a handful of data breaches, and the patience to follow each thread to its conclusion. That was all it took to go from an anonymous GitHub account to a full attribution.
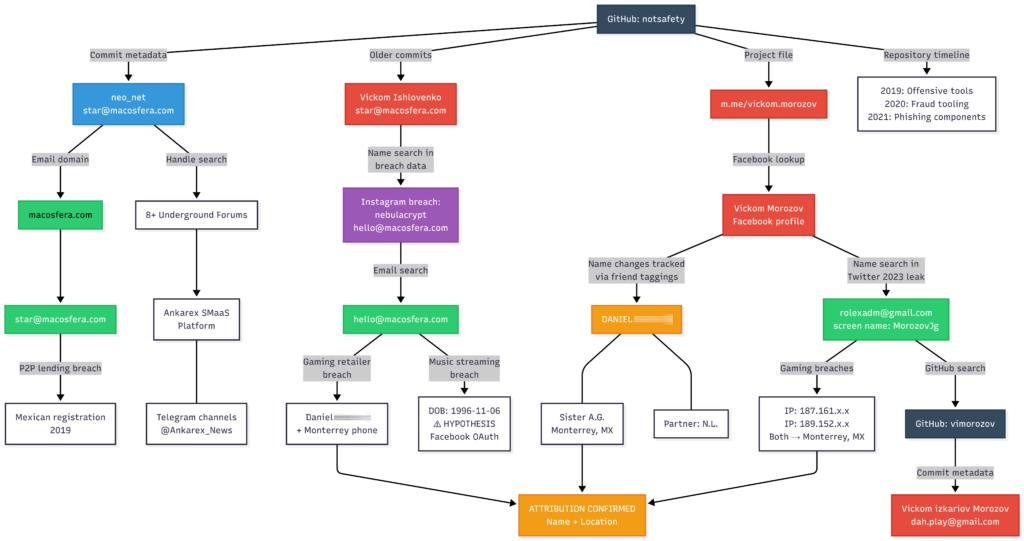
The Investigation at a Glance
The chart below summarizes the full attribution chain, showing how each finding led to the next, from the initial GitHub account to the confirmed real-world identity.
Conclusion
Every piece of evidence in this investigation came from open sources. The subject wasn’t undone by a sophisticated operation or privileged access, but by the kind of traces that everyone leaves and almost nobody thinks about cleaning up. A reused email here, a forgotten link there, an IP that shows up twice – none of it means much in isolation. The hard part is connecting it all, pulling threads across dozens of platforms and data sources until the picture comes together. That’s exactly the kind of work we built Zynap’s intelligence orchestrator to do, turning scattered, disconnected signals into structured attribution chains like the one you just read.
Appendix A: Full Alias and Email Listing
The following table documents all known aliases and email addresses attributed to the subject through the investigation. Each entry includes the source that established the link.
Email Addresses
| Source | |
| [email protected] | GitHub commit metadata (notsafety account) |
| [email protected] | Instagram breach (discovered by searching for “Ishlovenko Vickom,” linked to username nebulacrypt); also present in gaming retailer, music streaming service, and dark web intelligence platforms |
| [email protected] | Twitter 2023 leak (discovered by searching for “Vickom Morozov” — record: email [email protected], name “Vickom Morozov”, screen name MorozovJg, created May 2013); confirmed via gaming network and gaming platform breaches (IP overlap with Monterrey) |
| [email protected] | GitHub commit metadata (vimorozov account, discovered via [email protected]) |
| [email protected] | YouNow breach (discovered by searching for IP 187.161.***.***; record includes profile name “VickomMorozov” and Facebook ID) |
Aliases and Display Names
| Alias | Source |
| notsafety | GitHub account name |
| neo_net | GitHub commit metadata; underground forums (Breached, Cracked, XSS, BHF, Patched.to, Leakzone, Nulled, Hackforums); Telegram (@neo_net) |
| N€O N€Ť | Forum display name variant of neo_net (same registered accounts, stylized typography) |
| n3oxis | Mashacker.com 2020 breach (discovered by searching for [email protected]; forum username associated with that email) |
| Ankarex | Underground forums (dual handle with neo_net on same registered accounts); Telegram channels |
| Vickom Morozov | Facebook profile (tracked via friend taggings); project file Messenger link (m.me/vickom.morozov) |
| Vickom Ishlovenko | GitHub commit metadata (older commits); Facebook display name (name-change cycle) |
| Vickom izkariov Morozov | GitHub commit metadata (vimorozov account; commit author name associated with [email protected]) |
| VickomMorozov | Taringa breach (discovered by searching for [email protected]) |
| vimorozov | GitHub account, discovered via [email protected]; also appears as platform username in breach data |
| VMorozov | Taringa breach (discovered by searching for [email protected]) |
| MorozovJg | Twitter handle (associated with [email protected] and name “Vickom Morozov”) |
| nebulacrypt | Instagram breach (linked to [email protected] and name “Ishlovenko Vickom”) |
| dhlnx | Armor Games 2020 breach (discovered by searching for [email protected]; record includes IP 189.152.***.*** — Monterrey) |
| kikagain | foros.wow-colombia breach (discovered by searching for [email protected]; Spanish-language gaming forum) |
Appendix B: List of targets, Indicators of Compromise (IOCs), and TTPs
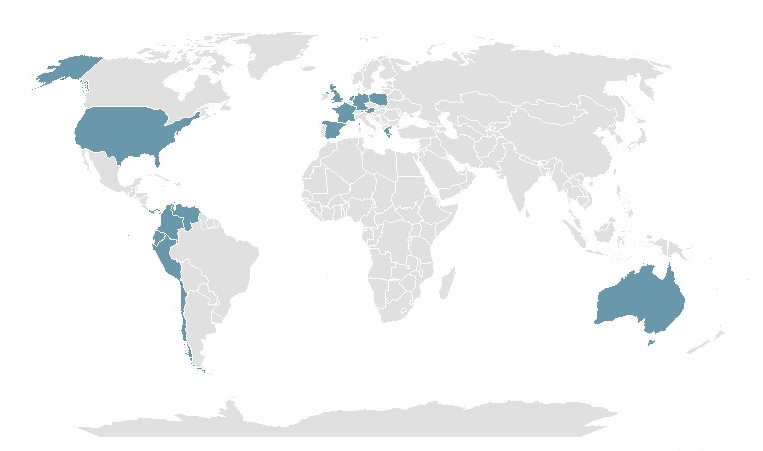
neo_net has been known to target the following victims, all belonging to the Financial Services sector, as stated in a previous campaign investigation:
Observed IOCs are the following:
| APK SHA-1 Hashes |
|---|
| de8929c1a0273d0ed0dc3fc55058e0cb19486b3c |
| b344fe1bbb477713016d41d996c0772a308a5146 |
| 8a099af61f1fa692f45538750d42aab640167fd2 |
| ab14161e243d478dac7a83086ed4839f8ad7ded8 |
| ded2655512de7d3468f63f9487e16a0bd17818ff |
| a5208de82def52b4019a6d3a8da9e14a13bc2c43 |
| 21112c1955d131fa6cab617a3d7265acfab783c2 |
| 6ea53a65fe3a1551988c6134db808e622787e7f9 |
| 62236a501e11d5fbfe411d841caf5f2253c150b8 |
| 7f0c3fdbfcdfc24c2da8aa3c52aa13f9b9cdda84 |
| f918a6ecba56df298ae635a6a0f008607b0420b9 |
| ffbcdf915916595b96f627df410722cee5b83f13 |
| 7b4ab7b2ead7e004c0d93fe916af39c156e0bc61 |
| 34d0faea99d94d3923d0b9e36ef9e0c48158e7a0 |
| e6c485551d4f209a0b7b1fa9aa78b7efb51be49b |
| 1df3ed2e2957efbd1d87aac0c25a3577318b8e2a |
| 6a907b8e5580a5067d9fb47ef21826f164f68f3f |
| 5d1c7ff3d16ec770cf23a4d82a91358b9142d21a |
| 86ad0123fa20b7c0efb6fe8afaa6a756a86c9836 |
| 14a36f18a45348ad9efe43b20d049f3345735163 |
| b506503bb71f411bb34ec8124ed26ae27a4834b9 |
| afe84fa17373ec187781f72c330dfb7bb3a42483 |
| 445468cd5c298f0393f19b92b802cfa0f76c32d4 |
| 8491ff15ad27b90786585b06f81a3938d5a61b39 |
| 2714e0744ad788142990696f856c5ffbc7173cf4 |
| 1ce0afe5e09b14f8aee6715a768329660e95121e |
| 96a3600055c63576be9f7dc97c5b25f1272edd2b |
| 9954ae7d31ea65cd6b8cbdb396e7b99b0cf833f4 |
| 07159f46a8adde95f541a123f2dda6c49035aad1 |
| ab19a95ef3adcb83be76b95eb7e7c557812ad2f4 |
| db8eeab4ab2e2e74a34c47ad297039485ff75f22 |
| dbf0cec18caabeb11387f7e6d14df54c808e441d |
| 69d38eed5dc89a7b54036cc7dcf7b96fd000eb92 |
| c38107addc00e2a2f5dcb6ea0cbce40400c23b49 |
| 279048e07c25fd75c4cef7c64d1ae741e178b35b |
| ef8c5d639390d9ba138ad9c2057524ff6e1398de |
| e7c2d0c80125909d85913dfb941bdc373d677326 |
| 145bd67f94698cc5611484f46505b3dc825bd6cd |
| Domains |
|---|
| ankarex[.]io |
| ankarex[.]net |
| macosfera[.]com |
| bbva.info-cliente[.]net |
| santander.esentregas[.]ga |
| bbva.esentregas[.]ga |
| correos.esentregas[.]ga |
| unicaja-movil-alertas[.]com |
| alertas-unicaja-banco[.]com |
| alertas-unicaja-seguridad[.]com |
| nbg-app-gr[.]com |
Here’s an overview of neo_net’s attributed Tactics, Techniques, and Procedures (TTPs):
| T1566.001: Phishing: Spearphishing Link |
| T1583.001: Acquire Infrastructure: Domains |
| T1583.003: Acquire Infrastructure: Virtual Private Server |
| T1071.001: Application Layer Protocol: Web Protocols |
| T1059.007: Command and Scripting Interpreter: JavaScript |
| T1059.004: Command and Scripting Interpreter: Unix Shell |
| T1590.005: Gather Victim Network Information: IP Addresses |
| T1056.003: Input Capture: Web Portal Capture |
| T1584.001: Compromise Infrastructure: Domains |
| T1102: Web Service |
| T1027: Obfuscated Files or Information |
| T1573: Encrypted Channel |
| T1406.002: Obfuscated Files or Information: Software Packing |
| T1633.001: Virtualization/Sandbox Evasion: System Checks |
| T1426: System Information Discovery |
| T1636.004: Protected User Data: SMS Messages |
| T1437.001: Application Layer Protocol: Web Protocols |
| T1481.003: Web Service: One-Way Communication |
| T1521.002: Encrypted Channel: Asymmetric Cryptography |
| T1646: Exfiltration Over C2 Channel |