This is the story of NINA AI, our agentic cybersecurity AI assistant, and how the intersection of coding agents, human engineering, and multi-agent orchestration is changing the rules of the game.
Layer 1: The Agent That Helps Us Build
Software development has changed. Our engineering team works side by side with coding agents that function as technical collaborators. They understand project context, propose implementations, write tests, and refactor code.
But the agent doesn’t replace the engineer. It amplifies them.
Domain knowledge remains human. What a cybersecurity workflow means, how a scripting node behaves in production, what a SOC analyst expects when investigating an incident. What the coding agent does is accelerate the translation of that knowledge into working software.
In practice, a small team can iterate at a speed that previously required much larger teams. We evaluate, adjust, evaluate again. The development cycle compresses without sacrificing quality.
The result of that human-agent collaboration is NINA AI.
Layer 2: NINA AI Under the Hood
NINA isn’t a chatbot with a language model behind it. It’s an orchestrated multi-agent system where a central agent coordinates specialists, each with their own tools, context, and objectives.
Orchestration With Intelligent Delegation
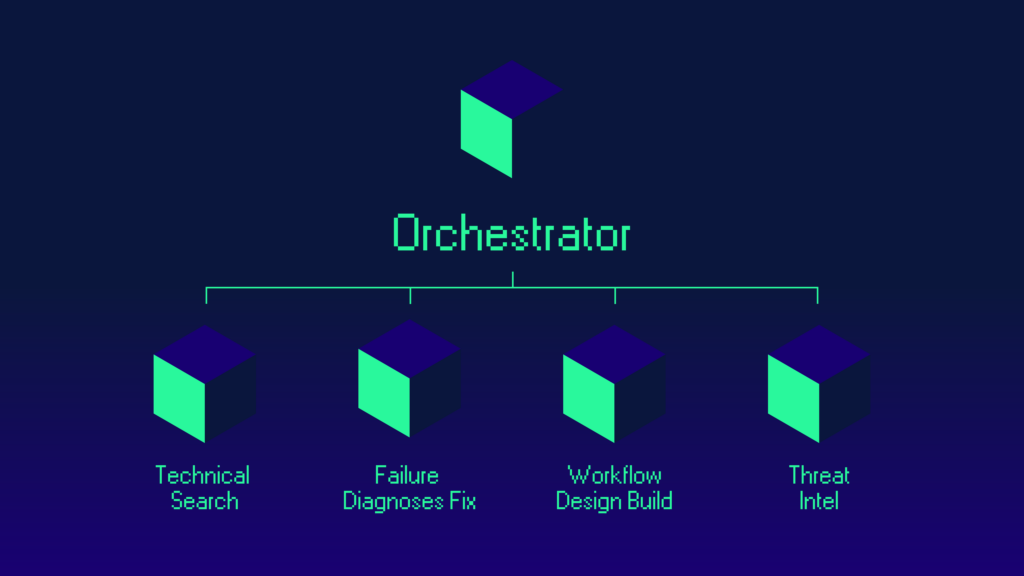
The orchestrator receives the query and decides: is it a documentation question? A failed workflow? A request to design an automation? Based on intent, it delegates to the right specialist.
Each sub-agent has its own set of tools (APIs, search engines, data access), specialized instructions for its domain, and the ability to collaborate with other sub-agents when the problem demands it.
Domain Knowledge Injected, Not Invented
NINA doesn’t rely solely on the language model to “know” cybersecurity. The system dynamically injects domain knowledge based on context.
When a user works with a reconnaissance workflow, malware analysis, or incident response, NINA detects the type and enriches the agent with relevant knowledge: common failure patterns, expected configurations, recommended tools.
This matters because the agent isn’t guessing. It operates with verified platform context. Fewer hallucinations, more precision.
Intelligence Analysis on Operational Data
A cybersecurity workflow that runs successfully can produce thousands of records: discovered assets, detected vulnerabilities, scanned certificates, threat intelligence API responses. The raw data is there. The problem is that nobody has time to review it all.
NINA does.
Volume
When a node produces a massive output — hundreds of exposed assets, thousands of DNS records, endless lists of open ports — NINA processes the full output and extracts what matters. It doesn’t truncate or blindly summarize. It analyzes with security judgment: how many of those assets have services exposed that shouldn’t be? Do the discovered subdomains suggest shadow IT? Is any certificate signed by a CA that has no business being there?
Interpretation, Not Data Dumps
The difference between a data dump and a useful report is judgment. NINA doesn’t tell you “47 subdomains were found.” It tells you that 3 of them resolve to IPs outside your corporate range and one exposes an admin panel without authentication. It prioritizes by criticality and flags what a human might miss in manual review.
Cross-Node Correlation
A scanner discovers assets, another module checks reputation, another verifies certificates. Each produces its own report. NINA connects the dots: the asset from the first node, with the low reputation from the second, and the expired certificate from the third. All on the same host. What manually requires opening three reports and cross-referencing in a spreadsheet comes out in the conversation.
On-Demand Analysis
Nothing needs to fail for NINA to step in. An analyst runs their usual recon workflow and asks NINA: “Analyze the results and tell me if there’s anything I should worry about.” NINA retrieves the execution, processes the outputs, and delivers a prioritized analysis. A second pair of eyes that never gets tired and always reviews with a threat mindset.
Diagnosis and Correction: From Hours to Minutes
When a cybersecurity workflow fails in production, response time matters. A threat detection pipeline that stops running at 3 AM can’t wait for someone to manually review logs the next morning.
NINA approaches this like a senior analyst would, but in seconds.
Full Context, Not Just The Error
NINA retrieves the entire execution, walks the node chain, and identifies where the flow broke and why. Expired credential? A filter that eliminated all results due to a misconfigured condition? An external service that returned an unexpected format? It distinguishes between a configuration failure, a data problem, and an infrastructure error, because the action is different in each case.
The Workflow That Doesn’t Fail But Doesn’t Work Either
Sometimes the flow finishes without errors but without results, or with incorrect results. For an analyst, that’s harder to diagnose than an explicit error. NINA inspects the actual output of each node, detects where data was lost or where a transformation twisted the result, and traces the problem to its origin.
Correction With The User In Control
Once the root cause is identified, NINA proposes the specific change: modify a parameter, update a credential, adjust a filter, reconnect a node. But it doesn’t touch anything without approval. The user reviews, accepts, and NINA applies the change directly on the workflow. Diagnosis and correction in the same conversation, without jumping between screens.
Closing The Loop
After the correction, NINA can launch a new execution and monitor the result. Detection, diagnosis, correction, verification. All in a single flow.
Workflow Construction With a Cybersecurity Mindset
Building a workflow isn’t connecting boxes. It’s making security architecture decisions: what gets scanned first, how information is enriched, which conditions trigger an alert versus an automated action, how to escalate when something needs human eyes.
NINA understands these decisions because it has domain knowledge, not just the ability to generate text.
From Objective To Design
The user says “I need to monitor SSL certificates on my exposed assets and alert before they expire.” NINA doesn’t look for a generic template. It decomposes the objective: asset discovery, certificate extraction, expiration date evaluation, criticality classification, alert routing by urgency. Each phase maps to actual nodes in the catalog.
Selection With Judgment
The platform has an extensive component catalog: attack surface scanners, threat intelligence queries, AI-powered scripting nodes, data transformations. NINA knows the capabilities and constraints of each one. It doesn’t put a brute force node where you need passive enrichment. It doesn’t connect an active scanner to a read-only source.
Real Branching Logic
Cybersecurity workflows are almost never linear. NINA designs conditional logic: if risk exceeds a threshold, escalate to incidents; if the asset is critical infrastructure, apply a different playbook; if data comes from an unverified source, validate before acting. Conditional nodes with concrete parameters, not free text for a model to interpret on the fly.
Agentic Nodes Where They Add Value
Some steps need more than fixed logic. An AI-powered scripting node can analyze the body of a phishing email and extract indicators of compromise. An intelligent transformation node can normalize data from sources with incompatible formats. NINA integrates these agentic components where they add real value, not to pad the workflow with AI.
Deterministic Execution
This is important: when NINA builds, it doesn’t “generate” freely. It works from a structured plan where each node is created with parameters validated against the platform catalog. The language model can’t invent configurations that don’t exist or connect incompatible components. Creativity lives in the design. Execution is precise.
Layer 3: The Recursion Is Real
This is where the three layers converge.
An AI agent (coding) helped build an AI agent (NINA). NINA designs, analyzes, and fixes cybersecurity workflows. Those workflows contain nodes that are, in turn, AI agents: intelligent scripting, data transformation, decision-making.
Three layers of agents. Each amplifying human capability at a different level:
- In development, the coding agent amplifies the engineer
- In operation, NINA amplifies the security analyst
- In execution, the agentic nodes amplify the workflow
And at every layer, the human remains in charge. The engineer decides the architecture. The analyst approves the correction. The operator defines the thresholds. AI doesn’t replace judgment. It scales it.
What Agentic Cybersecurity AI Means for Your Team
The cybersecurity talent shortage isn’t new. What is new is the ability to multiply every analyst’s effectiveness with systems that analyze data volumes no human could review manually, diagnose failures with full context, correct configurations in real time, and build automations with security judgment.
The SOC analyst who used to spend hours understanding why a workflow stopped working now gets diagnosis and correction in minutes. The team that generated hundreds of findings and only had time to review the first ten now has someone who processes everything and points to where to look. The team that took weeks to design a complex automation can now describe the objective and get a working workflow.
We’re not replacing analysts. We’re giving them superpowers.
A Reflection
When more years ago than my LinkedIn profile would like to admit, I was talking with my professors and classmates at university about intelligent agents, we did so from theory. Papers, whiteboard diagrams, and the promise that “someday” this would actually work. If I told them that today an agent helps me write code, that code is another agent, and that agent builds systems with more agents inside… they’d probably tell me to quit the science fiction and go back to studying for the exam.
Well, here we are.
The line between tool and collaborator is blurring. And in a domain as critical as cybersecurity, that’s not a luxury. It’s a necessity.
At Zynap, NINA is our bet on that future. A future that, as usually happens with technology, is already the present.
Zynap Inside AI is an ongoing series where our team shares what we’re building and learning. If you missed the earlier chapters, start with Chapter 1: The Agentic Wave and for the full series, head to Inside AI, here.