On February 28, 2026, US-Israeli cyber operations drove Iran’s internet connectivity to 4% of normal levels for over 60 hours, taking state media and IRGC communications offline. Israeli operators compromised the BadeSaba prayer app to push defection messages to millions of Iranian users. The Financial Times reported that Israeli intelligence had maintained long-term access to Tehran’s traffic camera network, which was used to support the targeting of the strike that killed Supreme Leader Khamenei. Eleven days later, Iran-aligned group Handala abused Microsoft Intune to remotely wipe roughly 200,000 devices belonging to medical technology company Stryker, disrupting surgical supply chains and emergency medical services.
These are not conventional military operations, and they don’t fit neatly into the categories that govern them. The U.S. Department of Defense designated cyberspace as an operational domain in 2011, and NATO followed at the 2016 Warsaw Summit, placing it alongside land, sea, air, and space. But the fifth domain operates by different rules. The same network access that serves intelligence collection can be repurposed for disruption with minimal additional investment. The thresholds for escalation are poorly defined. The norms governing proportional response remain contested. And attribution, the foundation of any deterrence framework, is inherently uncertain, because state actors exploit that uncertainty deliberately. They do this by operating through proxies, borrowing tooling from criminal groups, and planting forensic artifacts designed to mislead. When Poland disclosed a foiled attack on its National Centre for Nuclear Research, officials noted that entry vector indicators pointed to Iran but cautioned those could have been planted. Farsi-language metadata on a compromised server tells you what someone wanted you to find, not necessarily who was responsible.
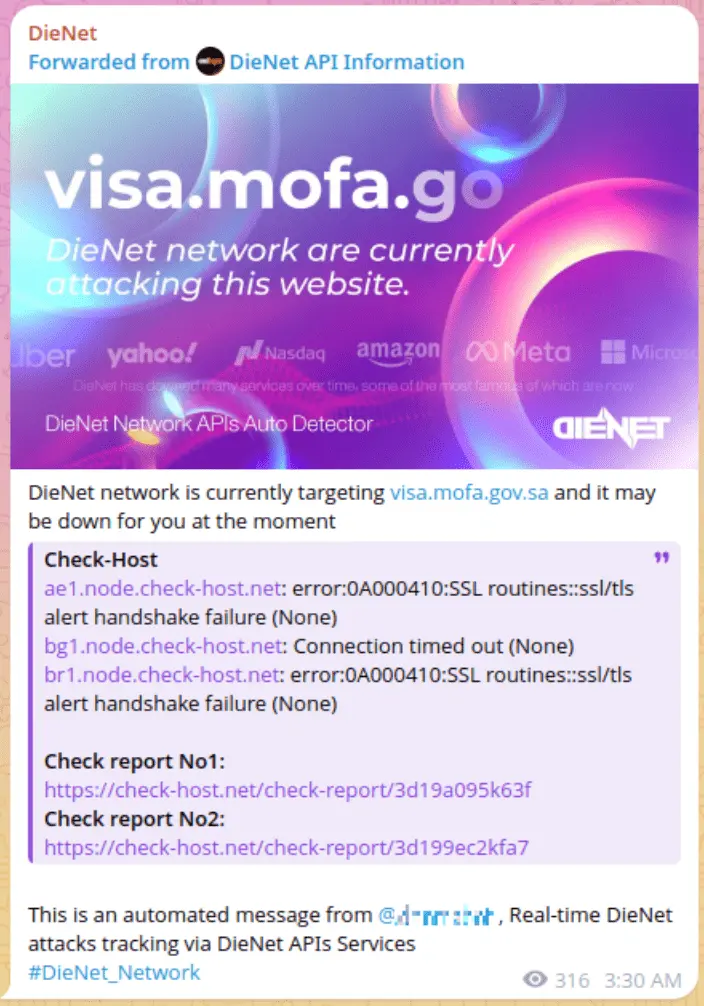
This is why the concept of “faketivism” matters: state-directed operations disguised as grassroots hacktivism, where a group claims ideological motivation, but its sophistication is inconsistent with volunteer collectives and its infrastructure traces back to intelligence services. Both sides of this conflict operate faketivist fronts: Iran does it through Handala and Cyber Av3ngers, while Israel does it through Predatory Sparrow (Gonjeshke Darande). States benefit from that ambiguity because it gives them both operational flexibility and plausible deniability.
The Asymmetry
The concept of proxy warfare maps directly onto how both sides have structured their cyber operations, but in radically different ways. Iran fields over 80 hacktivist groups alongside its state APT apparatus, namely MuddyWater, APT34, APT35, APT42, Handala/Void Manticore, and cybercriminal crossover operations like Pay2Key, a ransomware strain whose operational tempo rises and falls with geopolitical escalations. Many of these groups coordinate through an “Electronic Operations Room” announced on March 1, 2026, one day after the strikes began, by Cyber Islamic Resistance, a Shiite-aligned group. The groups range from GhostSec, which targets industrial control systems, to DieNet, which runs DDoS campaigns from a decentralized base with likely Russian membership and operates an automated system that broadcasts real-time attack status updates, giving its campaigns a level of operational branding unusual for hacktivist collectives. The underlying logic is volume and deniable distribution across dozens of semi-independent fronts; an approach Iran has developed over more than a decade as core doctrine.
A significant portion of these groups are Russian-speaking or explicitly pro-Russian, and their presence reflects a broader geopolitical partnership between Russia and Iran that has deepened through military cooperation, coordinated diplomatic positions, and shared opposition to the US-led international order. In practice, this translates into shared targeting lists, cross-promoted Telegram channels, and joint campaigns. The clearest illustration: in our collected Telegram activity, KillNet (prominent in the Russia-Ukraine war) posted on April 8 calling on supporters to “support the resistance of our brothers” in Iran, linking directly to the Cyber Islamic Resistance channel. Pro-Russian hacktivist infrastructure, built for one conflict, is being repurposed for another.
On the other side, there is no equivalent public-facing ecosystem of hacktivist or state-aligned groups operating in Israel’s name. Cyber operations aligned with Israel’s side have been reported (some of which are mentioned in the next part), but these operations are not accompanied by the kind of Telegram-based claim culture, public branding, or cross-group amplification that characterizes the pro-Iranian hacktivist landscape. The one exception is Predatory Sparrow, which functions as a faketivist front for sabotage operations against Iranian infrastructure. Beyond that, the pro-Israel cyber dimension remains largely invisible to open-source observers, which in itself tells us something about how the two sides have chosen to structure their operations.
The Expanding Target Map
Perhaps the most strategically significant pattern is how far the targeting extends beyond the countries actually at war. Hacktivist groups on both sides have targeted nations with no direct role in the fighting, and the justifications reveal a concentric logic: first the belligerents, then their allies, then their allies’ partners, then countries whose diplomatic statements or symbolic associations are deemed sufficient cause.
The following profiles are based on open-source research and Telegram activity collected during the preparation of this report.
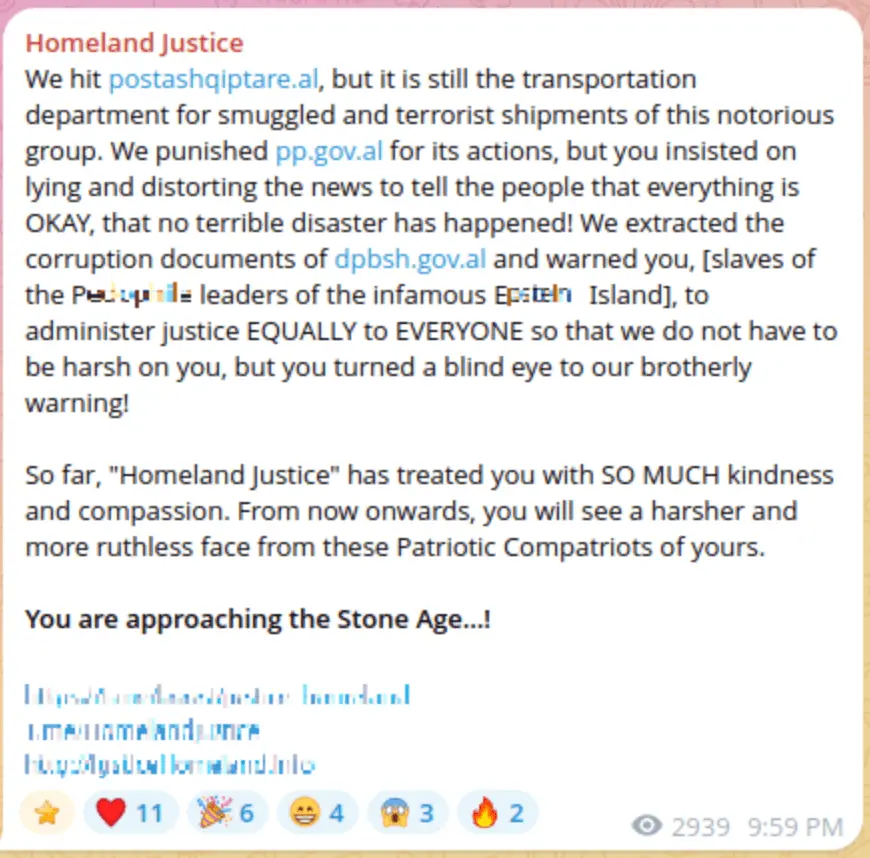
Golden Falcon
Pro-Iran, anti-Israel, anti-US. Unlike most hacktivist groups focused on DDoS or defacement, the group sits closer to open-source military intelligence than to traditional hacktivism.
Hider_Nex (Tunisian Maskers Cyber Force)
Pro-Palestinian, Tunisian origin. Launched the very first DDoS attack of the February 28 escalation.

This crosses from hacktivism into the distribution of targeting data with explicit incitement, a pattern shared with Golden Falcon.
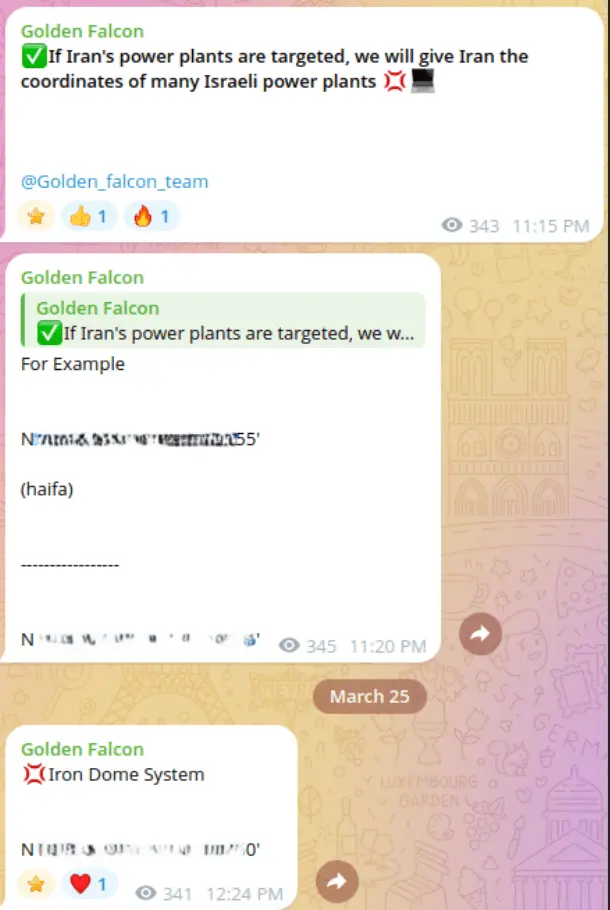
DieNet
Decentralized membership with likely Russian-speaking members. Emerged on Telegram in March 2025 and became the single most prolific pro-Iranian hacktivist group during the February-March 2026 escalation.

Targeted Gulf states from Kuwait to Bahrain for hosting US military bases or opening their airspace, extending the conflict’s cyber footprint well beyond the belligerents.
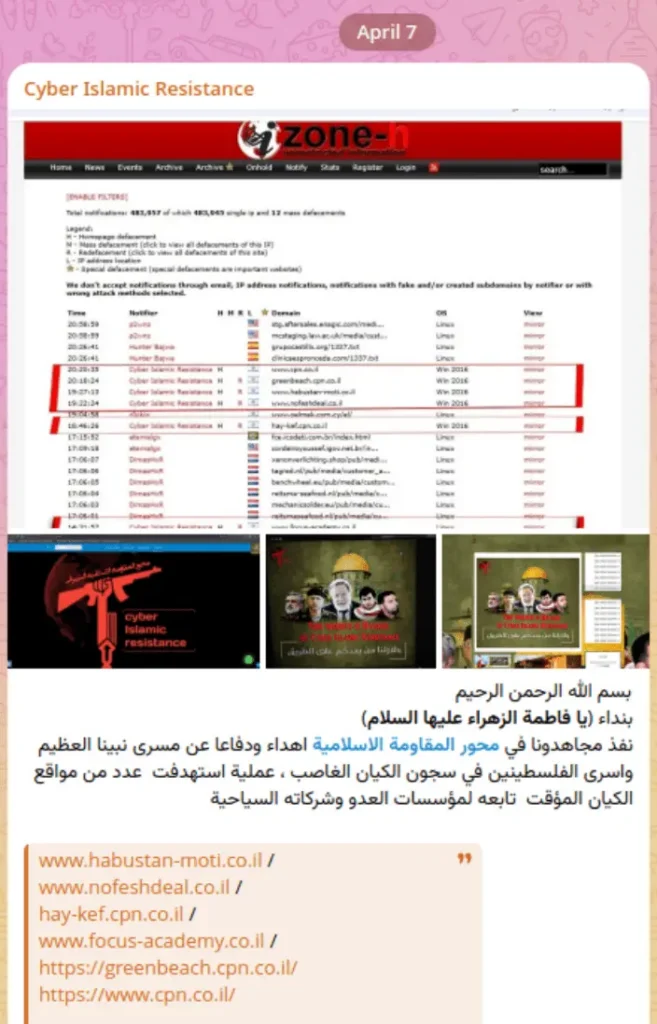
Cyber Islamic Resistance
Shiite-aligned, pro-Iran, linked to Iraqi groups. Announced the formation of the “Electronic Operations Room” on March 1, 2026 – the coordination hub for pro-Iranian hacktivist targeting.
KillNet / We Are KillNet
Pro-Russian, prominent in the Russia-Ukraine war, its symbolic role here matters: in our collected Telegram activity, the group posted on April 8 in Russian, calling on supporters to “support the resistance of our brothers” in Iran against “American and Israeli” adversaries, linking directly to the Cyber Islamic Resistance channel.

Sylhet Gang-SG
Pro-Palestinian, Bangladeshi origin. Active in both the Iran-Israel and India-Pakistan cyber conflicts. Promoted DieNet on its Telegram launch day, granting the new group immediate visibility. In our collected activity, Sylhet Gang-SG forwarded DieNet content about Gulf state targeting, justifying it because “their hosting of the US forced us to target them.” The group illustrates how South and Southeast Asian collectives plug into Middle Eastern cyber conflicts through ideological alignment rather than geographic proximity.

BD Anonymous
Pro-Palestinian, Bangladeshi. Issued a direct warning to Armenia threatening offensive operations against Armenian infrastructure for “supporting the Zionist regime and cooperating with the U.S.”

This is the outer ring of the concentric targeting logic: countries with no direct involvement in the conflict.
Botnet Kingdom / Coup Team
Anti-Israel (#OpIsrael). Claimed to have taken down the websites of Mizrahi-Tefahot Bank and the Bank of Israel.
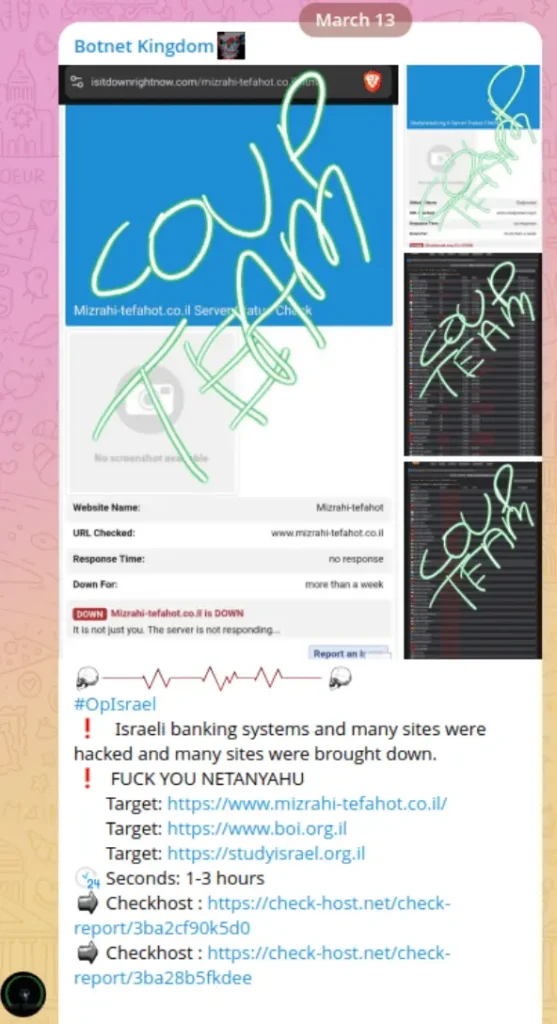
Crude messaging and unclear structure, but the targeting of major financial institutions reflects the broader pattern of going after high-visibility symbols.
Anonymous Syria Hackers
Syrian, anti-Iran. One of the very few hacktivist groups vocally operating on the pro-Israel side of the conflict, as the group operates in Arabic and explicitly frames its operations as resistance against the Iranian regime. Running a sustained #OP_IRAN campaign with branded imagery.

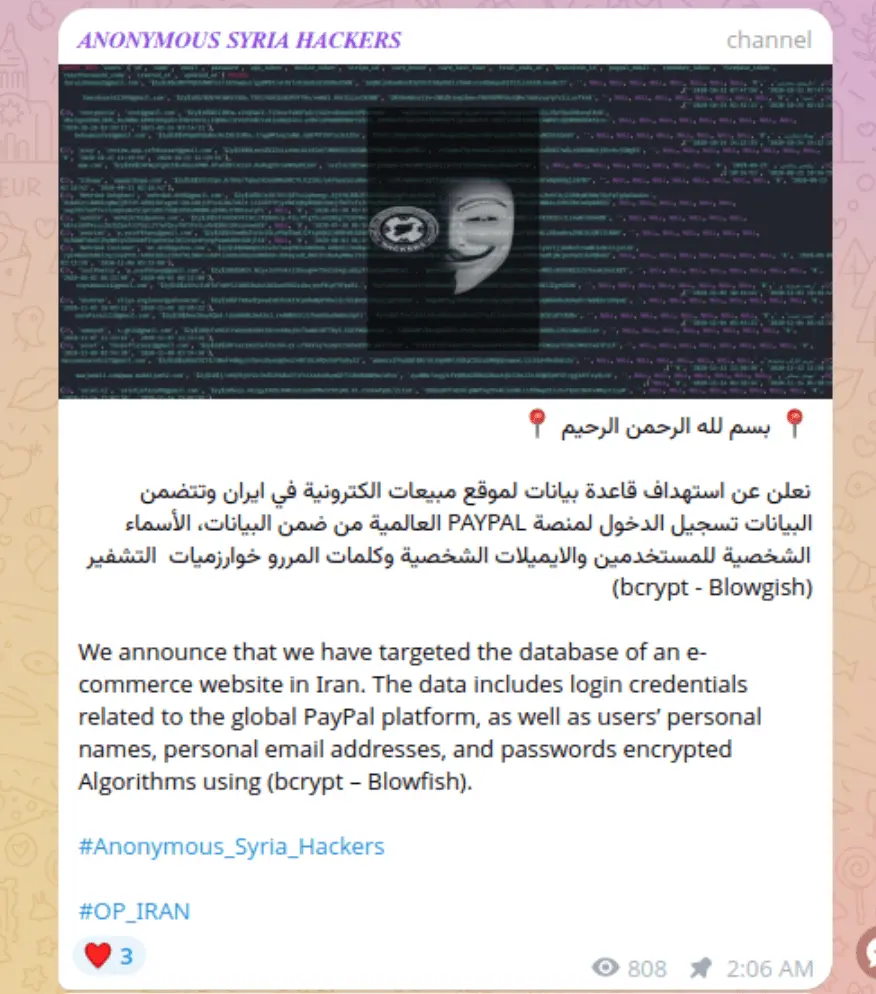

In our collected activity, the group breached an Iranian e-commerce database containing PayPal credentials and encrypted passwords, and targeted an Iranian educational institution linked to Khamenei supporters, leaking personal certificates, national ID numbers, and photographs.
Conclusion
The fifth domain has not respected the boundaries of the kinetic conflict. Groups operating from Bangladesh threaten Armenia. A Tunisian collective launched the conflict’s first cyberattack. Russian-speaking operators coordinate through shared Telegram channels. The attribution problem that makes all this possible, the same problem that lets states hide behind proxies and plant false flags, also means that the expanding target map has no natural stopping point. For any country that assumes it is not a party to this war, the evidence collected here suggests otherwise.
Zynia Labs
This report is part of Zynia Labs’ ongoing threat intelligence research. For more from the team, take a look here.